RC0-501 Online Practice Questions and Answers
When designing a web based client server application with single application server and database cluster backend, input validation should be performed:
A. On the client
B. Using database stored procedures
C. On the application server
D. Using HTTPS
Which of the following would enhance the security of accessing data stored in the cloud? (Select TWO)
A. Block level encryption
B. SAML authentication
C. Transport encryption
D. Multifactor authentication
E. Predefined challenge questions
F. Hashing
A help desk is troubleshooting user reports that the corporate website is presenting untrusted certificate errors to employees and customers when they visit the website. Which of the following is the MOST likely cause of this error, provided the certificate has not expired?
A. The certificate was self signed, and the CA was not imported by employees or customers
B. The root CA has revoked the certificate of the intermediate CA
C. The valid period for the certificate has passed, and a new certificate has not been issued
D. The key escrow server has blocked the certificate from being validated
A mobile device user is concerned about geographic positioning information being included in messages sent between users on a popular social network platform. The user turns off the functionality in the application, but wants to ensure the
application cannot re-enable the setting without the knowledge of the user.
Which of the following mobile device capabilities should the user disable to achieve the stated goal?
A. Device access control
B. Location based services
C. Application control
D. GEO-Tagging
A network operations manager has added a second row of server racks in the datacenter. These racks face the opposite direction of the first row of racks. Which of the following is the reason the manager installed the racks this way?
A. To lower energy consumption by sharing power outlets
B. To create environmental hot and cold isles
C. To eliminate the potential for electromagnetic interference
D. To maximize fire suppression capabilities
In a corporation where compute utilization spikes several times a year, the Chief Information Officer (CIO) has requested a cost-effective architecture to handle the variable capacity demand. Which of the following characteristics BEST describes what the CIO has requested?
A. Elasticity
B. Scalability
C. High availability
D. Redundancy
A botnet has hit a popular website with a massive number of GRE-encapsulated packets to perform a DDoS attack. News outlets discover a certain type of refrigerator was explogted and used to send outbound packets to the website that crashed. To which of the following categories does the refrigerator belong?
A. SoC
B. ICS
C. IoT
D. MFD
Ann, a security administrator, has been instructed to perform fuzz-based testing on the company's applications. Which of the following best describes what she will do?
A. Enter random or invalid data into the application in an attempt to cause it to fault
B. Work with the developers to eliminate horizontal privilege escalation opportunities
C. Test the applications for the existence of built-in- back doors left by the developers
D. Hash the application to verify it won't cause a false positive on the HIPS.
When identifying a company's most valuable assets as part of a BIA, which of the following should be the FIRST priority?
A. Life
B. Intellectual property
C. Sensitive data
D. Public reputation
An auditor is reviewing the following output from a password-cracking tool:
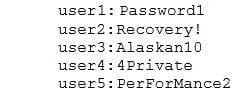
Which of the following methods did the auditor MOST likely use?
A. Hybrid
B. Dictionary
C. Brute force
D. Rainbow table

