PSE-STRATA Online Practice Questions and Answers
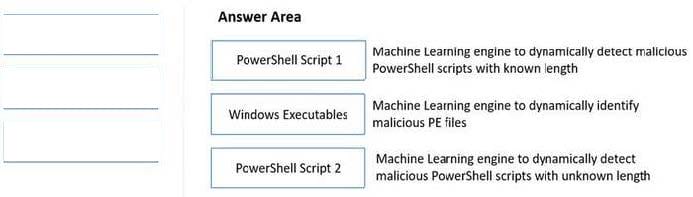
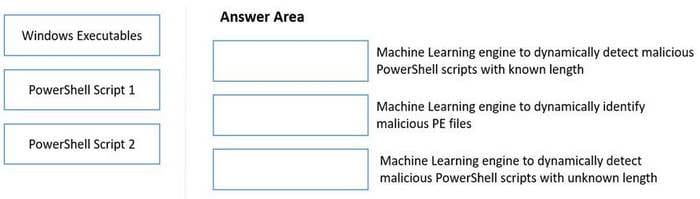
DRAG DROP
Match the WildFire Inline Machine Learning Model to the correct description for that model.
Select and Place:
Which built-in feature of PAN-OS allows the NGFW administrator to create a policy that provides autoremediation for anomalous user behavior and malicious activity while maintaining user visibility?
A. Dynamic user groups (DUGS)
B. tagging groups
C. remote device User-ID groups
D. dynamic address groups (DAGs)
Which are the three mandatory components needed to run Cortex XDR? (Choose three.)
A. Panorama
B. NGFW with PANOS 8 0.5 or later
C. Cortex Data Lake
D. Traps
E. Pathfinder
F. Directory Syn Service
A client chooses to not block uncategorized websites. Which two additions should be made to help provide some protection? (Choose two.)
A. A URL filtering profile with the action set to continue for unknown URL categories to security policy rules that allow web access
B. A data filtering profile with a custom data pattern to security policy rules that deny uncategorized websites
C. A file blocking profile attached to security policy rules that allow uncategorized websites to help reduce the risk of drive by downloads
D. A security policy rule using only known URL categories with the action set to allow
WildFire can discover zero-day malware in which three types of traffic? (Choose three)
A. SMTP
B. HTTPS
C. FTP
D. DNS
E. TFTP
There are different Master Keys on Panorama and managed firewalls.
What is the result if a Panorama Administrator pushes configuration to managed firewalls?
A. The push operation will fail regardless of an error or not within the configuration itself
B. Provided there's no error within the configuration to be pushed, the push will succeed
C. The Master Key from the managed firewalls will be overwritten with the Master Key from Panorama
D. There will be a popup to ask if the Master Key from the Panorama should replace the Master Key from the managed firewalls
When log sizing is factored for the Cortex Data Lake on the NGFW, what is the average log size used in calculation?
A. 8MB
B. depends on the Cortex Data Lake tier purchased
C. 18 bytes
D. 1500 bytes
Select the BOM for the Prisma Access, to provide access for 5500 mobile users and 10 remote locations (100Mbps each) for one year, including Base Support and minimal logging. The customer already has 4x PA5220r 8x PA3220,1x Panorama VM for 25 devices.
A. 5500x PAN-GPCS-USER-C-BAS-1YR, 1000x PAN-GPCS-NET-B-BAS-1YR, 1x PAN-LGS-1TB-1YR
B. 5500x PAN-GPCS-USER-C-BAS-1YR, 1000x PAN-GPCS-NET-B-BAS-1YR, 1x PAN-SVC-BAS-PRA-25. 1x PAN-PRA-25
C. 5500x PAN-GPCS-USER-C-BAS-1YR, 1000x PAN-GPCS-NET-B-BAS-1YRr 1x PAN-LGS-1TB-1YR, 1x PAN-PRA-25, 1x PAN-SVC-BAS-PRA-25
D. 1x PAN-GPCS-USER-C-BAS-1YR, 1x PAN-GPCS-NET-B-BAS-1YR, 1x PAN-LGS-1TB-1YR
For customers with high bandwidth requirements for Service Connections, what two limitations exist when onboarding multiple Service Connections to the same Prisma Access location servicing a single Datacenter? (Choose two.)
A. Network segments in the Datacenter need to be advertised to only one Service Connection
B. The customer edge device needs to support policy-based routing with symmetric return functionality
C. The resources in the Datacenter will only be able to reach remote network resources that share the same region
D. A maximum of four service connections per Datacenter are supported with this topology
What are two advantages of the DNS Sinkholing feature? (Choose two.)
A. It forges DNS replies to known malicious domains.
B. It monitors DNS requests passively for malware domains.
C. It can be deployed independently of an Anti-Spyware Profile.
D. It can work upstream from the internal DNS server.