PCNSA Online Practice Questions and Answers
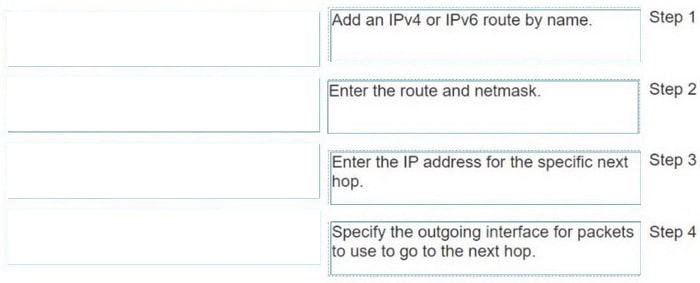
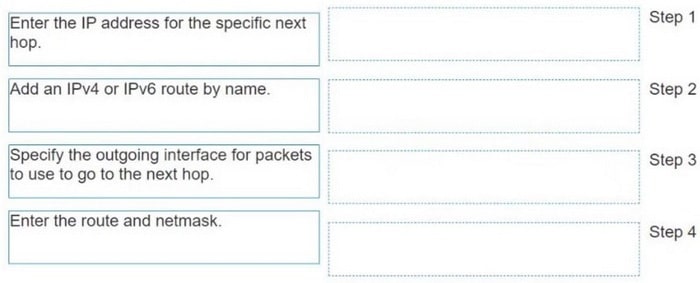
DRAG DROP
Drag the steps into the correct order to create a static route.
Select and Place:
Prior to a maintenance-window activity, the administrator would like to make a backup of only the running configuration to an external location. What command in Device > Setup > Operations would provide the most operationally efficient way to achieve this outcome?
A. save named configuration snapshot
B. export device state
C. export named configuration snapshot
D. save candidate config
Given the scenario, which two statements are correct regarding multiple static default routes when they are configured as shown in the image? (Choose two.)
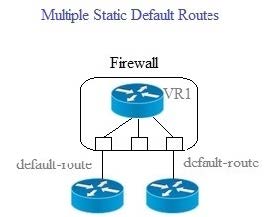
A. Path monitoring does not determine if route is useable
B. Route with highest metric is actively used
C. Path monitoring determines if route is useable
D. Route with lowest metric is actively used
Access to which feature requires a URL Filtering license?
A. PAN-DB database
B. External dynamic lists
C. DNS Security
D. Custom URL categories
Which URL Filtering Profile action does not generate a log entry when a user attempts to access a URL?
A. override
B. allow
C. block
D. continue
How many zones can an interface be assigned with a Palo Alto Networks firewall?
A. two
B. three
C. four
D. one
Which verdict may be assigned to a WildFire sample?
A. Phishing
B. Spyware
C. PUP
D. Malware
To protect against illegal code execution, which Security profile should be applied?
A. Antivirus profile on allowed traffic
B. Antivirus profile on denied traffic
C. Vulnerability Protection profile on allowed traffic
D. Vulnerability Protection profile on denied traffic
With the PAN-OS 11.0 Nova release, which two attack options can new inline deep learning analysis engines detect and prevent? (Choose two.)
A. Command injection attacks
B. SSL attacks
C. SQL injection attacks
D. HTTP attacks
How are service routes used in PAN-OS?
A. By the OSPF protocol, as part of Dijkstra's algorithm, to give access to the various services offered in the network
B. To statically route subnets so they are joinable from, and have access to, the Palo Alto Networks external services
C. For routing, because they are the shortest path selected by the BGP routing protocol
D. To route management plane services through data interfaces rather than the management interface