PCCET Online Practice Questions and Answers
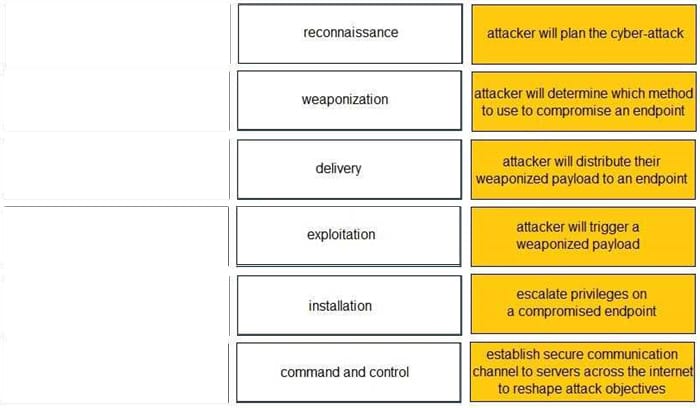
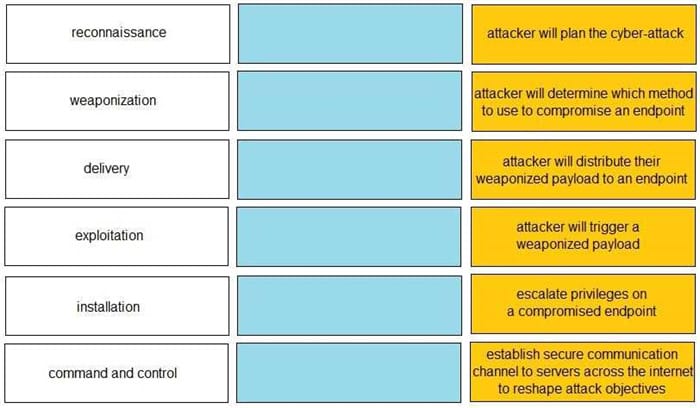
DRAG DROP
Given the graphic, match each stage of the cyber-attack lifecycle to its description.

Select and Place:
During the OSI layer 3 step of the encapsulation process, what is the Protocol Data Unit (PDU) called when the IP stack adds source (sender) and destination (receiver) IP addresses?
A. Frame
B. Segment
C. Packet
D. Data
When signature-based antivirus software detects malware, what three things does it do to provide protection? (Choose three.)
A. decrypt the infected file using base64
B. alert system administrators
C. quarantine the infected file
D. delete the infected file
E. remove the infected file's extension
Which type of Software as a Service (SaaS) application provides business benefits, is fast to deploy, requires minimal cost and is infinitely scalable?
A. Benign
B. Tolerated
C. Sanctioned
D. Secure
Which pillar of Prisma Cloud application security addresses ensuring that your cloud resources and SaaS applications are correctly configured?
A. visibility, governance, and compliance
B. network protection
C. dynamic computing
D. compute security
In which situation would a dynamic routing protocol be the quickest way to configure routes on a router?
A. the network is large
B. the network is small
C. the network has low bandwidth requirements
D. the network needs backup routes
Which type of Wi-Fi attack depends on the victim initiating the connection?
A. Evil twin
B. Jasager
C. Parager
D. Mirai
What is the primary security focus after consolidating data center hypervisor hosts within trust levels?
A. control and protect inter-host traffic using routers configured to use the Border Gateway Protocol (BGP) dynamic routing protocol
B. control and protect inter-host traffic by exporting all your traffic logs to a sysvol log server using the User Datagram Protocol (UDP)
C. control and protect inter-host traffic by using IPv4 addressing
D. control and protect inter-host traffic using physical network security appliances
What is a characteristic of the National Institute Standards and Technology (NIST) defined cloud computing model?
A. requires the use of only one cloud service provider
B. enables on-demand network services
C. requires the use of two or more cloud service providers
D. defines any network service
Which product from Palo Alto Networks extends the Security Operating Platform with the global threat intelligence and attack context needed to accelerate analysis, forensics, and hunting workflows?
A. Global Protect
B. WildFire
C. AutoFocus
D. STIX