NSE7_ATP-2.5 Online Practice Questions and Answers
Examine the Suspicious Indicators section of the scan job shown in the exhibit, then answer the following question:
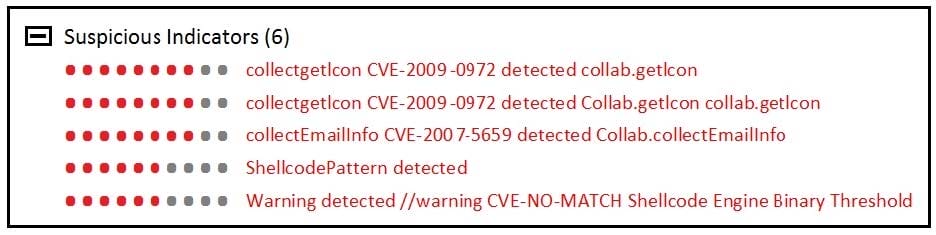
Which FortiSandbox component identified the vulnerability exploits?
A. VM scan
B. Antivirus scan
C. Static analysis
D. Cache check
Which advanced threat protection integration solution should you use to protect against out-of-band attack vectors, such as USB drives, used during the delivery stage of the kill chain?
A. FortiGate and FortiSandbox
B. FortiMail and FortiSandbox
C. FortiWeb and FortiSandbox
D. FortiClient and FortiSandbox
Which of the following scan job report sections are generated by static analysis? (Choose two.)
A. Office Behaviors
B. Launched Processes
C. Registry Changes
D. Virtual Simulator
FortiSandbox generates structured threat information exchange (STIX) packages for which of the following threats? (Choose two.)
A. Botnet connections
B. Malware
C. Intrusion attempts
D. Malicious URLs
Which FortiSandbox interfaces can you use for sniffer mode? (Choose two.)
A. port2
B. port3
C. port1
D. port4
What information does a scan job report include? (Choose two.)
A. Updates to the antivirus database
B. Summary of the file activity
C. Details about system files deleted of modified
D. Changes to the FortiSandbox configuration
Examine the CLI configuration, than answer the following question:
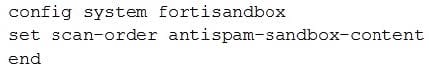
Which of the following statements is true regarding this FortiMail's inspection behavior?
A. Malicious URLs will be removed by antispam and replaced with a message.
B. Suspicious files not detected by antivirus will be inspected by FortiSandbox.
C. Known malicious URLs will be inspected by FortiSandbox.
D. Files are skipped by content profile will be inspected by FortiSandbox.
What advantage does sandboxing provide over traditional virus detection methods?
A. Heuristics detection that can detect new variants of existing viruses.
B. Pattern-based detection that can catch multiple variants of a virus.
C. Full code execution in an isolated and protected environment.
D. Code emulation as packets are handled in real-time.
Examine the scan job report shown in the exhibit, then answer the following question: Which of the following statements are true regarding this verdict? (Choose two.)
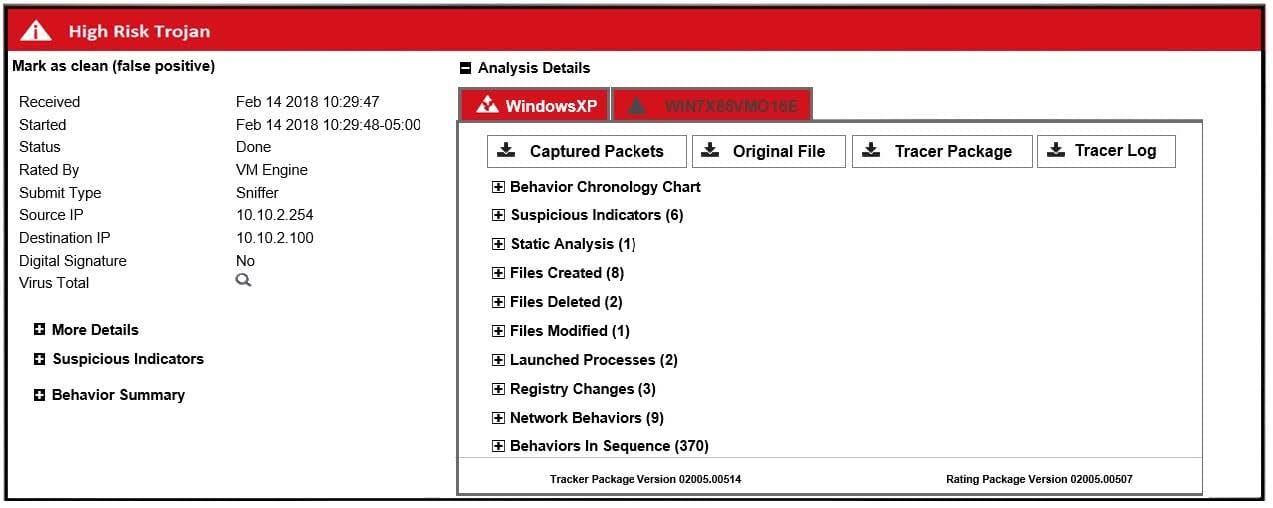
A. The file contained malicious JavaScipt.
B. The file contained a malicious macro.
C. The file was sandboxed in two-guest VMs.
D. The file was extracted using sniffer-mode inspection.
Examine the following topology shown in the exhibit, then answer the following question: Which of the following configuration tasks are applicable to secure Webserver from known threats? (Choose two.)
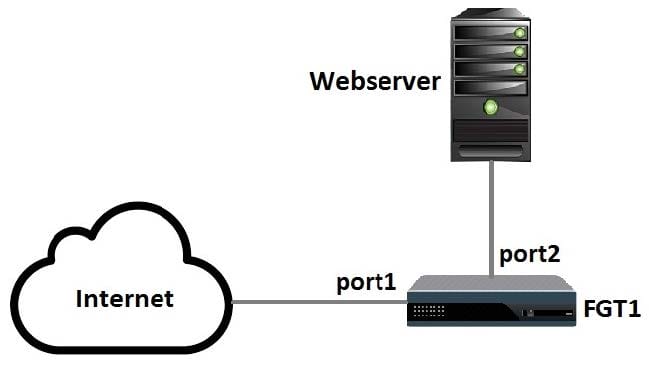
A. Apply an SSL inspection profile configured for protecting SSL server.
B. Apply an antivirus profile to the port1 -> port2 firewall policy.
C. Apply an SSL inspection profile configured for full SSL inspection.
D. Apply a web filter profile to the port1 -> port2 firewall policy.

