NSE6_FNC-8.5 Online Practice Questions and Answers
Which three circumstances trigger Layer 2 polling of infrastructure devices? (Choose three.)
A. A matched security policy
B. Scheduled poll timings
C. Linkup and Linkdown traps
D. Manual polling
E. A failed Layer 3 poll
What agent is required in order to detect an added USB drive?
A. Mobile
B. Passive
C. Dissolvable
D. Persistent
Which system group will force at-risk hosts into the quarantine network, based on point of connection?
A. Forced Quarantine
B. Forced Remediation
C. Forced Isolation
D. Physical Address Filtering
In which view would you find who made modifications to a Group?
A. The Admin Auditing view
B. The Alarms view
C. The Event Management view
D. The Security Events view
Which two agents can validate endpoint compliance transparently to the end user? (Choose two.)
A. Persistent
B. Dissolvable
C. Mobile
D. Passive
Which command line shell and scripting language does FortiNAC use for WinRM?
A. Powershell
B. Bash
C. Linux
D. DOS
Refer to the exhibit, and then answer the question below.
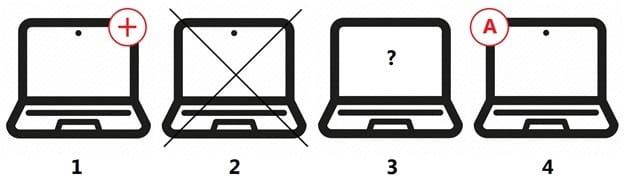
Which host is rogue?
A. 4
B. 2
C. 3
D. 1
When you create a user or host profile; which three criteria can you use? (Choose three.)
A. An applied access policy
B. Administrative group membership
C. Location
D. Host or user group memberships
E. Host or user attributes
Which agent can receive and display messages from FortiNAC to the end user?
A. Persistent
B. Passive
C. MDM
D. Dissolvable
Where do you look to determine when and why the FortiNAC made an automated network access change?
A. The Admin Auditing view
B. The Event view
C. The Connections view
D. The Port Changes view

