NSE5_FCT-7.0 Online Practice Questions and Answers
A FortiClient EMS administrator has enabled the compliance rule for the sales department. Which Fortinet device will enforce compliance with dynamic access control?
A. FortiClient
B. FortiClient EMS
C. FortiGate
D. FortiAnalyzer
Refer to the exhibit.
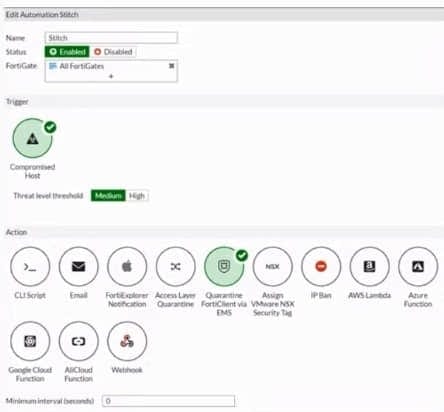
Based on the Security Fabric automation settings, what action will be taken on compromised endpoints?
A. Endpoints will be quarantined through EMS
B. Endpoints will be banned on FortiGate
C. An email notification will be sent for compromised endpoints
D. Endpoints will be quarantined through FortiSwitch
Refer to the exhibits.
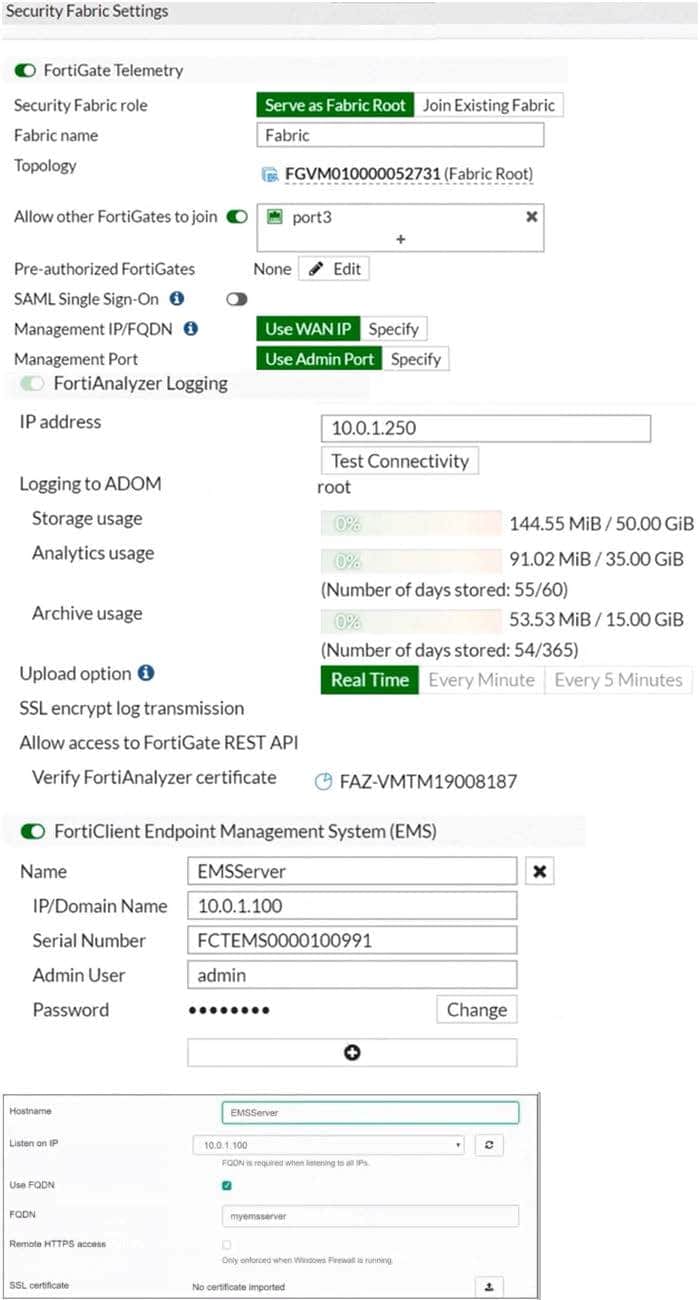
Based on the FortiGate Security Fabric settings shown in the exhibits, what must an administrator do on the EMS server to successfully quarantine an endpoint. when it is detected as a compromised host (loC)?
A. The administrator must enable remote HTTPS access to EMS.
B. The administrator must enable FQDN on EMS.
C. The administrator must authorize FortiGate on FortiAnalyzer.
D. The administrator must enable SSH access to EMS.
An administrator installs FortiClient on Windows Server. What is the default behavior of real-time protection control?
A. Real-time protection must update AV signature database
B. Real-time protection sends malicious files to FortiSandbox when the file is not detected locally
C. Real-time protection is disabled
D. Real-time protection must update the signature database from FortiSandbox
An administrator is required to maintain a software vulnerability on the endpoints, without showing the feature on the FortiClient dashboard. What must the administrator do to achieve this requirement?
A. Disable select the vulnerability scan feature in the deployment package
B. Use the default endpoint profile
C. Select the vulnerability scan feature in the deployment package, but disable the feature on the endpoint profile
D. Click the hide icon on the vulnerability scan tab
Refer to the exhibit.
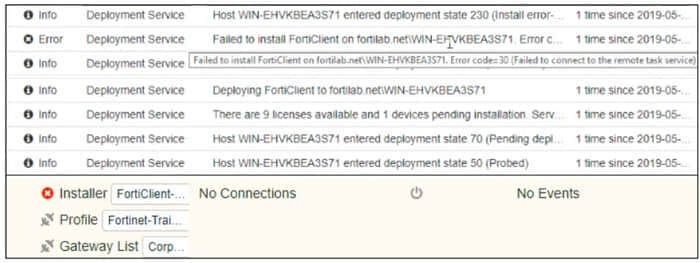
Based on the logs shown in the exhibit, why did FortiClient EMS fail to install FortiClient on the endpoint?
A. The remote registry service is not running
B. The Windows installer service is not running
C. The task scheduler service is not running.
D. The FortiClient antivirus service is not running
Refer to the exhibit.
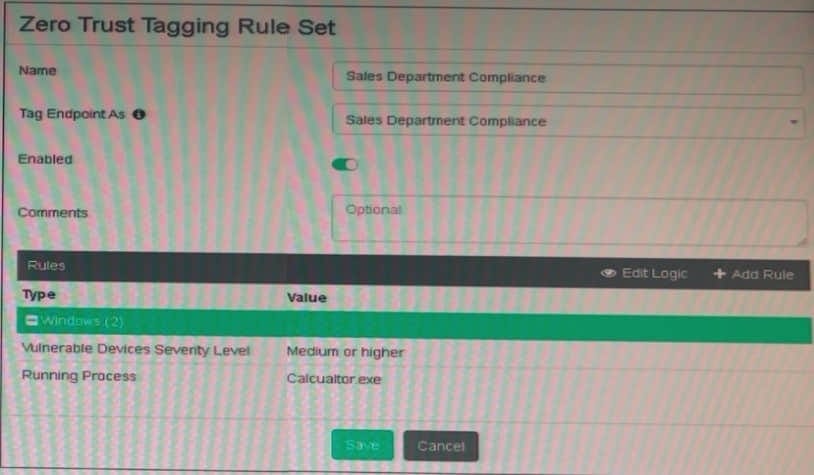
Based on the settings shown in the exhibit, which two actions must the administrator take to make the endpoint compliant? (Choose two.)
A. Enable the webfilter profile
B. Integrate FortiSandbox for infected file analysis
C. Patch applications that have vulnerability rated as high or above
D. Run Calculator application on the endpoint
Which two statements are true about ZTNA? (Choose two.)
A. ZTNA provides role-based access
B. ZTNA manages access for remote users only
C. ZTNA manages access through the client only
D. ZTNA provides a security posture check
Refer to the exhibit.
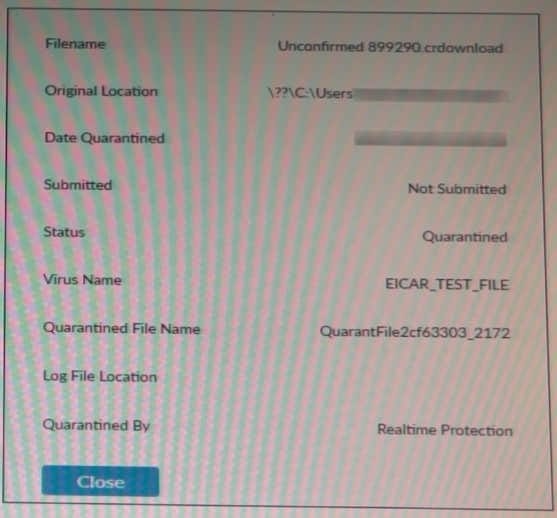
Based on the FortiClient log details shown in the exhibit, which two statements are true? (Choose two.)
A. The file status is Quarantined
B. The filename is sent to ForuSandbox for further inspection.
C. The file location IS \??\D:\Users\.
D. The filename is Unconfirmed 899290 .crdownload.
Refer to the exhibits.
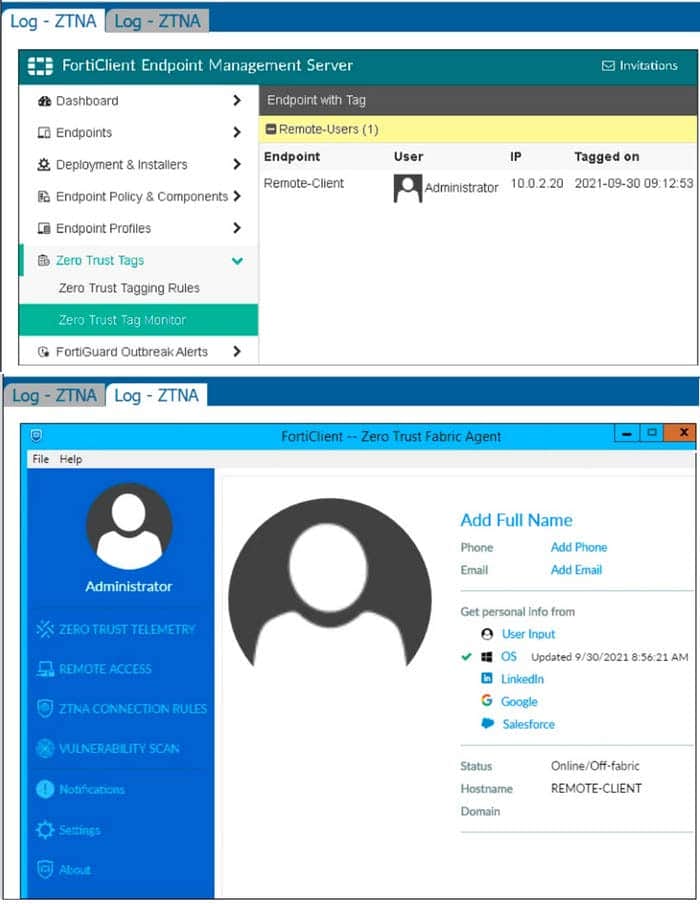
Which show the Zero Trust Tag Monitor and the FortiClient GUI status.
Remote-Client is tagged as Remote-Users on the FortiClient EMS Zero Trust Tag Monitor.
What must an administrator do to show the tag on the FortiClient GUI?
A. Update tagging rule logic to enable tag visibility
B. Change the FortiClient system settings to enable tag visibility
C. Change the endpoint control setting to enable tag visibility
D. Change the user identity settings to enable tag visibility

