NSE5_EDR-5.0 Online Practice Questions and Answers
Which scripting language is supported by the FortiEDR action managed?
A. TCL
B. Python
C. Perl
D. Bash
Which security policy has all of its rules disabled by default?
A. Device Control
B. Ransomware Prevention
C. Execution Prevention
D. Exfiltration Prevention
What is the role of a collector in the communication control policy?
A. A collector blocks unsafe applications from running
B. A collector is used to change the reputation score of any application that collector runs
C. A collector records applications that communicate externally
D. A collector can quarantine unsafe applications from communicating
A company requires a global communication policy for a FortiEDR multi-tenant environment.
How can the administrator achieve this?
A. An administrator creates a new communication control policy and shares it with other organizations
B. A local administrator creates new a communication control policy and shares it with other organizations
C. A local administrator creates a new communication control policy and assigns it globally to all organizations
D. An administrator creates a new communication control policy for each organization
Which two statements about the FortiEDR solution are true? (Choose two.)
A. It provides pre-infection and post-infection protection
B. It is Windows OS only
C. It provides central management
D. It provides pant-to-point protection
Refer to the exhibit.
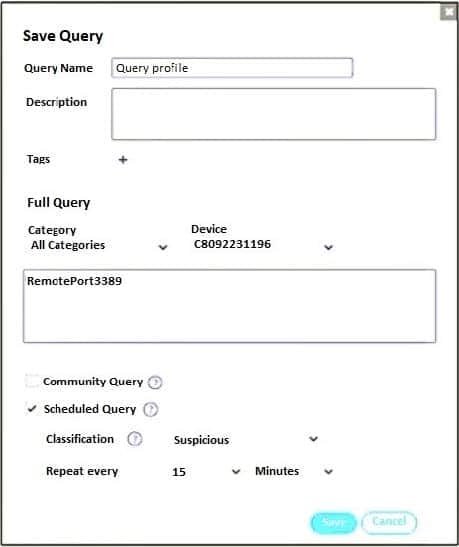
Based on the threat hunting query shown in the exhibit which of the following is true?
A. RDP connections will be blocked and classified as suspicious
B. A security event will be triggered when the device attempts a RDP connection
C. This query is included in other organizations
D. The query will only check for network category
Which two statements are true about the remediation function in the threat hunting module? (Choose two.)
A. The file is removed from the affected collectors
B. The threat hunting module sends the user a notification to delete the file
C. The file is quarantined
D. The threat hunting module deletes files from collectors that are currently online.
FortiXDR relies on which feature as part of its automated extended response?
A. Playbooks
B. Security Policies
C. Forensic
D. Communication Control
Which three steps does FortiXDR perform to find and prevent cyberattacks? (Choose three.)
A. Extended analysis
B. Extended detection
C. Extended discovery
D. Extended investigation
E. Extended response
Which statement is true about the flow analyzer view in forensics?
A. It displays a graphic flow diagram.
B. Two events can be compared side-by-side.
C. It shows details about processes and sub processes.
D. The stack memory of a specific device can be retrieved

