NSE4_FGT-6.0 Online Practice Questions and Answers
What files are sent to FortiSandbox for inspection in flow-based inspection mode?
A. All suspicious files that do not have their hash value in the FortiGuard antivirus signature database.
B. All suspicious files that are above the defined oversize limit value in the protocol options.
C. All suspicious files that match patterns defined in the antivirus profile.
D. All suspicious files that are allowed to be submitted to FortiSandbox in the antivirus profile.
An administrator has configured central DNAT and virtual IPs. Which of the following can be selected in the firewall policy Destination field?
A. A VIP group
B. The mapped IP address object of the VIP object
C. A VIP object
D. An IP pool
Which statement about FortiGuard services for FortiGate is true?
A. The web filtering database is downloaded locally on FortiGate.
B. Antivirus signatures are downloaded locally on FortiGate.
C. FortiGate downloads IPS updates using UDP port 53 or 8888.
D. FortiAnalyzer can be configured as a local FDN to provide antivirus and IPS updates.
You are configuring the root FortiGate to implement the security fabric. You are configuring port10 to communicate with a downstream FortiGate. View the default Edit Interface in the exhibit below: When configuring the root FortiGate to communicate with a downstream FortiGate, which settings are required to be configured? (Choose two.)
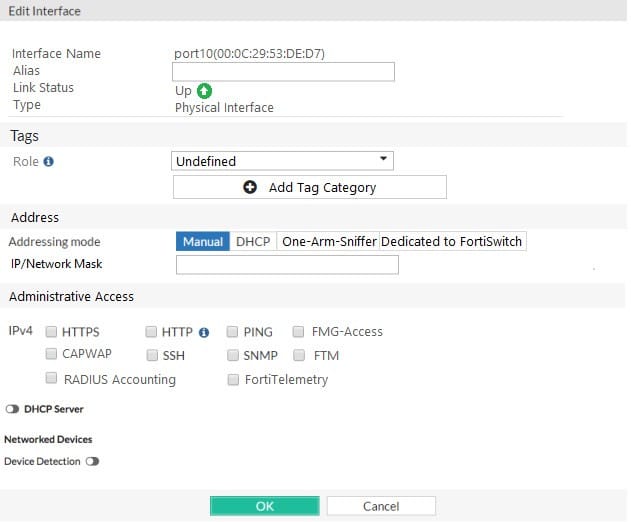
A. Device detection enabled.
B. Administrative Access: FortiTelemetry.
C. IP/Network Mask.
D. Role: Security Fabric.
Which of the following statements about policy-based IPsec tunnels are true? (Choose two.)
A. They can be configured in both NAT/Route and transparent operation modes.
B. They support L2TP-over-IPsec.
C. They require two firewall policies: one for each directions of traffic flow.
D. They support GRE-over-IPsec.
When override is enabled, which of the following shows the process and selection criteria that are used to elect the primary FortiGate in an HA cluster?
A. Connected monitored ports > HA uptime > priority > serial number
B. Priority > Connected monitored ports > HA uptime > serial number
C. Connected monitored ports > priority > HA uptime > serial number
D. HA uptime > priority > Connected monitored ports > serial number
Which statements about HA for FortiGate devices are true? (Choose two.)
A. Sessions handled by proxy-based security profiles cannot be synchronized.
B. Virtual clustering can be configured between two FortiGate devices that have multiple VDOMs.
C. HA management interface settings are synchronized between cluster members.
D. Heartbeat interfaces are not required on the primary device.
Examine the exhibit, which shows the partial output of an IKE real-time debug.
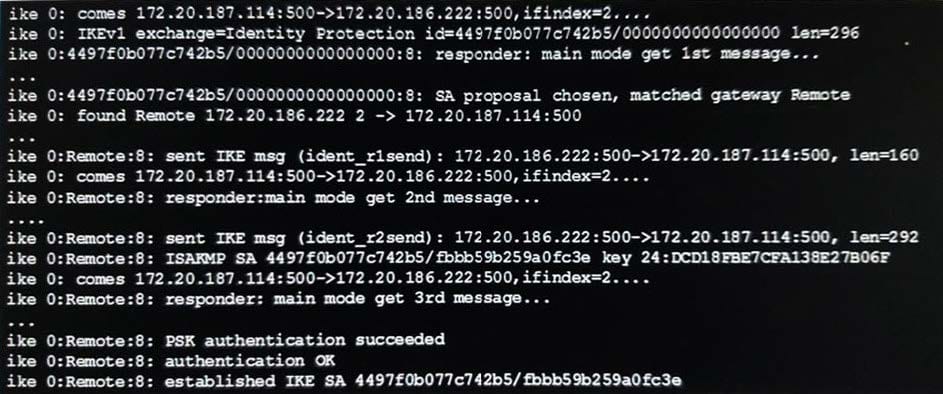
Which of the following statement about the output is true?
A. The VPN is configured to use pre-shared key authentication.
B. Extended authentication (XAuth) was successful.
C. Remote is the host name of the remote IPsec peer.
D. Phase 1 went down.
You have tasked to design a new IPsec deployment with the following criteria:
1.
There are two HQ sues that all satellite offices must connect to
2.
The satellite offices do not need to communicate directly with other satellite offices
3.
No dynamic routing will be used
4.
The design should minimize the number of tunnels being configured.
Which topology should be used to satisfy all of the requirements?
A. Partial mesh
B. Hub-and-spoke
C. Fully meshed
D. Redundant
View the exhibit.
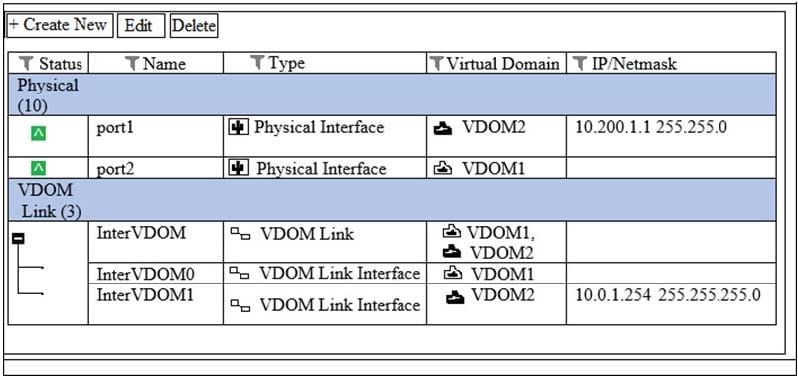
VDOM1 is operating in transparent mode VDOM2 is operating in NAT Route mode. There is an inteface VDOM link between both VDOMs. A client workstation with the IP address 10.0.1.10/24 is connected to port2. A web server with the IP address 10.200.1.2/24 is connected to port1. What is required in the FortiGate configuration to route and allow connections from the client workstation to the web server? (Choose two.)
A. A static or dynamic route in VDOM2 with the subnet 10.0.1.0/24 as the destination.
B. A static or dynamic route in VDOM1 with the subnet 10.200.1.0/24 as the destination.
C. One firewall policy in VDOM1 with port2 as the source interface and InterVDOM0 as the destination interface.
D. One firewall policy in VDOM2 with InterVDOM1 as the source interface and port1 as the destination interface.

