NSE4_FGT-5.6 Online Practice Questions and Answers
Which of the following statements are true about route-based IPsec VPNs?
(Choose two.)
Response:
A. A virtual IPsec interface is automatically created after a phase 1 is added to the configuration
B. They require firewall policies with the Action set to IPsec
C. They support L2TP-over-IPsec tunnels
D. They can be created in transparent mode VDOMs
What protocol can be used to dynamically assign an IP address to a physical interface? Response:
A. PPPoE
B. IP Config
C. BOOTP
D. ICMP
Which statement is true about split tunneling in SSL VPN? Response:
A. It is supported in web-only mode.
B. It can be enabled by the SSL VPN user, after connecting to the SSL VPN.
C. If enabled, Internet traffic uses the local gateway of the connecting host.
D. If disabled, SSL VPN users must authenticate using FortiToken.
How are the application control signatures updated on a FortiGate device? Response:
A. By running the application control auto-learning feature.
B. Through FortiGuard updates.
C. By upgrading the FortiOS firmware to a newer release.
D. By clicking Update Signatures in the application control profile.
Examine the log message attributes. Which statements are correct?
(Choose two.)
hostname=www.youtube.com profiletype="Webfilter_Profile"
profile="default"
status="passthrough"
msg="URL belongs to a category with warnings enabled"
Response:
A. The website was allowed on the first attempt
B. The user failed authentication
C. The category action was set to warning.
D. The user was prompted whether to proceed or go back.
Which of the following statements is true regarding client integrity checking in SSL VPN? Response:
A. It detects the Windows client security applications running in the SSL VPN client's PCs.
B. It validates the SSL VPN user credentials on the remote authentication server.
C. It verifies which SSL VPN portal must be presented to each SSL VPN user.
D. It verifies that the latest SSL VPN client is installed in the client's PC.
What is the purpose of the Policy Lookup feature? Response:
A. It searches the matching policy based on input criteria.
B. It creates packet flow over FortiGate by sending real-time traffic.
C. It finds duplicate objects in firewall policies.
D. It creates a new firewall policy based on input criteria.
Examine the exhibit, which shows the output of a web filtering real time debug.
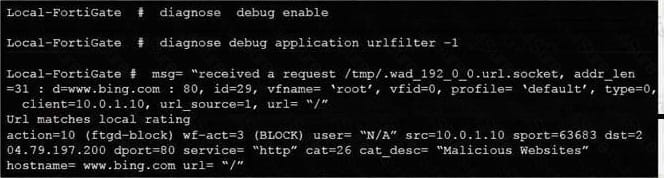
Why is the site www.bing.com being blocked? Response:
A. The web server IP address 204.79.197.200 is categorized by FortiGuard as Malicious Websites.
B. The rating for the web site www.bing.com has been locally overridden to a category that is being blocked.
C. The web site www.bing.com is categorized by FortiGuard as Malicious Websites.
D. The user has not authenticated with the FortiGate yet.
Which statements about high availability (HA) for FortiGates are true?
(Choose two.)
Response:
A. Virtual clustering can be configured between two FortiGate devices with multiple VDOM.
B. Heartbeat interfaces are not required on the primary device.
C. HA management interface settings are synchronized between cluster members.
D. Sessions handled by UTM proxy cannot be synchronized.
Examine the following log message attributes and select two correct statements from the list below.
(Choose two.)
Response:
A. The category action was set to warning.
B. The website was allowed on the first attempt.
C. The user was prompted to decide whether to proceed or go back.
D. The user failed authentication.

