JN0-333 Online Practice Questions and Answers
What are three characteristics of session-based forwarding, compared to packet-based forwarding, on an SRX Series device? (Choose three.)
A. Session-based forwarding uses stateful packet processing.
B. Session-based forwarding requires less memory.
C. Session-based forwarding performs faster processing of existing session.
D. Session-based forwarding uses stateless packet processing,
E. Session-based forwarding uses six tuples of information.
Click the Exhibit button.
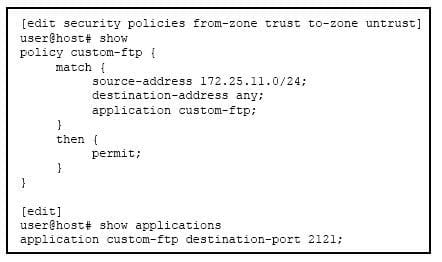
Users at a remote office are unable to access an FTP server located at the remote corporate data center as expected. The remote FTP server is listening on the non-standard TCP port 2121.
Referring to the exhibit, what is causing the problem?
A. The FTP clients must be configured to listen on non-standard client ports for the FTP data channel negotiations to succeed.
B. Two custom FTP applications must be defined to allow bidirectional FTP communication through the SRX Series device.
C. The custom FTP application definition does not have the FTP ALG enabled.
D. A new security policy must be defined between the untrust and trust zones.
What are the maximum number of redundancy groups that would be used on a chassis cluster?
A. The maximum number of redundancy groups use is equal to the number of configured physical interfaces.
B. The maximum number of redundancy groups use is equal to one more than the number of configured physical interfaces.
C. The maximum number of redundancy groups use is equal to the number of configured logical interfaces.
D. The maximum number of redundancy groups use is equal to one more than the number of configured logical interfaces.
Clients at a remote office are accessing a website that is against your company Internet policy. You change the action of the security policy that controls HTTP access from permit to deny on the remote office SRX Series device. After committing the policy change, you notice that new users cannot access the website but users that have existing sessions on the device still have access. You want to block all user sessions immediately.
Which change would you make on the SRX Series device to accomplish this task?
A. Add the set security flow tcp-session rst-invalidate-session option to the configuration and commit the change.
B. Add the set security policies policy-rematch parameter to the configuration and commit the change.
C. Add the security flow tcp-session strict-syn-check option to the configuration and commit the change.
D. Issue the commit full command from the top of the configuration hierarchy.
You are asked to support source NAT for an application that requires that its original source port not be changed.
Which configuration would satisfy the requirement?
A. Configure a source NAT rule that references an IP address pool with interface proxy ARP enabled.
B. Configure the egress interface to source NAT fixed-port status.
C. Configure a source NAT rule that references an IP address pool with the port no-translation parameter enabled.
D. Configure a source NAT rule that sets the egress interface to the overload status.
Which two statements are true when implementing source NAT on an SRX Series device? (Choose two.)
A. Source NAT is applied before the security policy search.
B. Source NAT is applied after the route table lookup.
C. Source NAT is applied before the route table lookup.
D. Source NAT is applied after the security policy search.
You recently configured an IPsec VPN between two SRX Series devices. You notice that the Phase 1 negotiation succeeds and the Phase 2 negotiation fails.
Which two configuration parameters should you verify are correct? (Choose two.)
A. Verify that the IKE gateway proposals on the initiator and responder are the same.
B. Verify that the VPN tunnel configuration references the correct IKE gateway.
C. Verify that the IPsec policy references the correct IKE proposals.
D. Verify that the IKE initiator is configured for main mode.
Which action will restrict SSH access to an SRX Series device from a specific IP address which is connected to a security zone named trust?
A. Implement a firewall filter on the security zone trust.
B. Implement a security policy from security zone junos-host to security zone trust.
C. Implement host-inbound-traffic system-services to allow SSH.
D. Implement a security policy from security zone trust to security zone junos-host.
Click to the Exhibit button.
Referring to the exhibit, which two statements are true? (Choose two.)
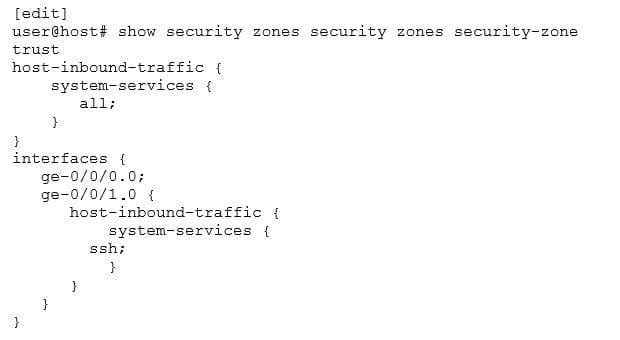
A. Interface ge-0/0/0 will not accept SSH connections.
B. Interfaces ge-0/0/0.0 and ge-0/0/1.0 will allow SSH connections.
C. Interface ge-0/0/0.0 will respond to pings.
D. Interface ge-0/0/1.0 will respond to pings.
Click the Exhibit button. Referring to the exhibit, what will happen if client 172.16.128.50 tries to connect to destination 192.168.150.3 using HTTP?
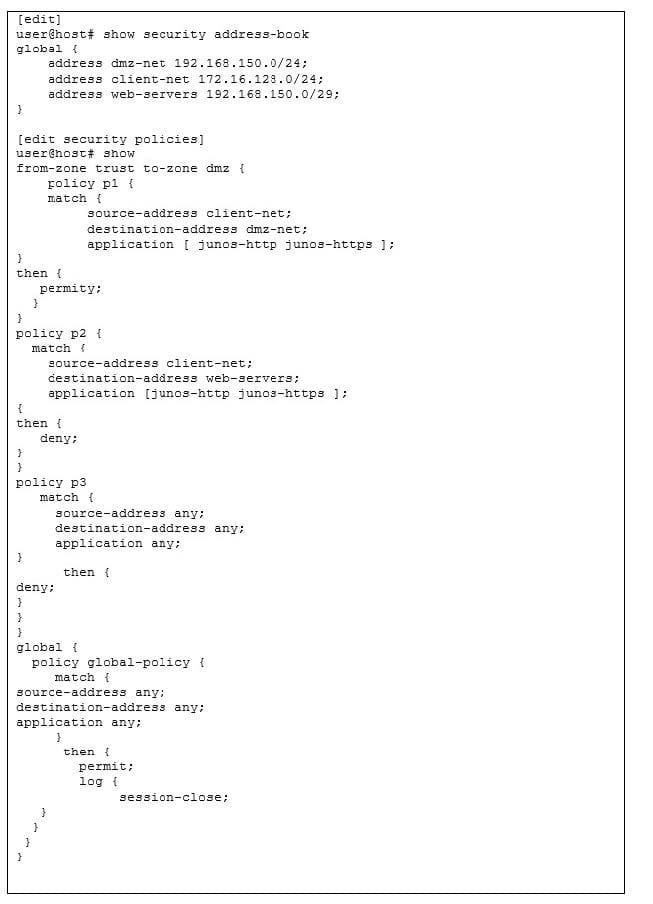
A. The client will be permitted by policy p1.
B. The client will be denied by policy p3.
C. The client will be denied by policy p2.
D. The client will be permitted by the global policy.

