JN0-332 Online Practice Questions and Answers
You want to create an out-of-band management zone and assign the ge-0/0/0.0 interface to that zone. From the [edit] hierarchy, which command do you use to configure this assignment?
A. set security zones management interfaces ge-0/0/0.0
B. set zones functional-zone management interfaces ge-0/0/0.0
C. set security zones functional-zone management interfaces ge-0/0/0.0
D. set security zones functional-zone out-of-band interfaces ge-0/0/0.0
Which parameters are valid SCREEN options for combating operating system probes?
A. syn-fin, syn-flood, and tcp-no-frag
B. syn-fin, port-scan, and tcp-no-flag
C. syn-fin, fin-no-ack, and tcp-no-frag
D. syn-fin, syn-ack-ack-proxy, and tcp-no-frag
You have configured your chassis cluster to include redundancy group 1. Node 0 is configured to be the primary node for this redundancy group. You need to verify that the redundancy group failover is successful.
Which command do you use to manually test the failover?
A. request chassis cluster manual failover group 1 node 1
B. request cluster failover redundancy-group 1 node 1
C. request chassis cluster manual failover redundancy-group 1 node 1
D. request chassis cluster failover redundancy-group 1 node 1
Which three statements are true when working with high-availability clusters? (Choose three.)
A. The valid cluster-id range is between 0 and 255.
B. Junos OS security devices can belong to more than one cluster if cluster virtualization is enabled.
C. If the cluster-id value is set to 0 on a Junos security device, the device will not participate in the cluster.
D. A reboot is required if the cluster-id or node value is changed.
E. Junos OS security devices can belong to one cluster only.
What is the purpose of a zone in JUNOS Software?
A. A zone defines a group of security devices with a common management.
B. A zone defines the geographic region in which the security device is deployed.
C. A zone defines a group of network segments with similar security requirements.
D. A zone defines a group of network segments with similar class-of-service requirements.
You want to show interface-specific zone information and statistics. Which operational command would be used to accomplish this?
A. show security zones detail
B. show interfaces ge-0/0/3.0
C. show interfaces terse
D. show interfaces ge-0/0/3.0 extensive
You need to build a scheduler to apply to a policy that will allow traffic from Monday to Friday only.
What will accomplish this task?
A. [edit schedulers] user@host# show scheduler no-weekends { daily all-day; sunday exclude; saturday exclude; }
B. [edit schedulers] user@host# show scheduler no-weekends { daily except weekends; }
C. [edit schedulers] user@host# show scheduler no-weekends { daily; sunday exclude; saturday exclude; }
D. [edit schedulers] user@host# show scheduler no-weekends { weekday all-day; }
Which three actions should be used when initially implementing Junos Screen options? (Choose three.)
A. Deploy Junos Screen options only in functional zones.
B. Deploy Junos Screen options only in vulnerable security zones.
C. Understand the behavior of legitimate applications.
D. Use the limit-session option.
E. Use the alarm-without-drop option.
What are three types of reconnaissance attacks? (Choose three)
A. IP address sweep
B. Port scanning
C. Denial of service
D. IP options
E. Teardrop
Click the Exhibit button.
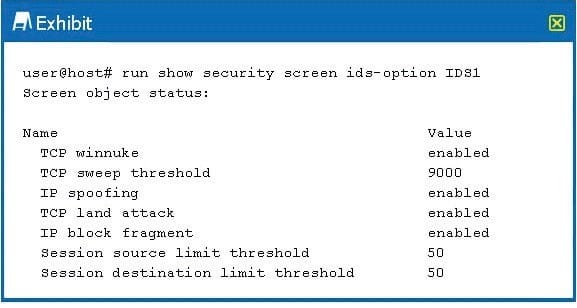
You are testing the IP spoofing screen on your SRX Series device. The ids-option IDS1 is shown in the
exhibit, but no IP spoofingmessagesareseeninthelogs.
What is happening?
A. The IP block fragment must be disabled for IP spoofing to be detected.
B. IDS is not applied to the correct security policy.
C. IDS1 is not applied to the correct security zone.
D. The TCP sweep threshold must be lowered to l000 to allow enough time for the spoof attack.

