JN0-230 Online Practice Questions and Answers
Which two segments describes IPsec VPNs? (Choose two.)
A. IPsec VPN traffic is always authenticated.
B. IPsec VPN traffic is always encrypted.
C. IPsec VPNs use security to secure traffic over a public network between two remote sites.
D. IPsec VPNs are dedicated physical connections between two private networks.
Which three actions would be performed on traffic traversing an IPsec VPAN? (Choose three.)
A. Port forwarding
B. Authentication
C. Encryption
D. Deep inspection
E. Payload verification
Which security object defines a source or destination IP address that is used for an employee Workstation?
A. Zone
B. Screen
C. Address book entry
D. scheduler
What are two characteristic of static NAT SRX Series devices? (Choose two.)
A. Source and destination NAT rules take precedence over static NAT rules.
B. A reverse mapping rule is automatically created for the source translation.
C. Static NAT rule take precedence over source and destination NAT rules.
D. Static rules cannot coexist with destination NAT rules on the same SRX Series device configuration.
Which two statements are true regarding zone-based security policies? (Choose two.)
A. Zone-based policies must reference a source address in the match criteria.
B. Zone-based policies must reference a URL category in the match criteria.
C. Zone-based policies must reference a destination address in the match criteria
D. Zone-based policies must reference a dynamic application in the match criteria.
You verify that the SSH service is configured correctly on your SRX Series device, yet administrators attempting to connect through a revenue port are not able to connect. In this scenario, what must be configured to solve this problem?
A. A security policy allowing SSH traffic.
B. A host-inbound-traffic setting on the incoming zone
C. An MTU value target than the default value
D. A screen on the internal interface
Which zone is considered a functional zone?
A. Trust
B. Junos host
C. Null
D. Management
Click the Exhibit button
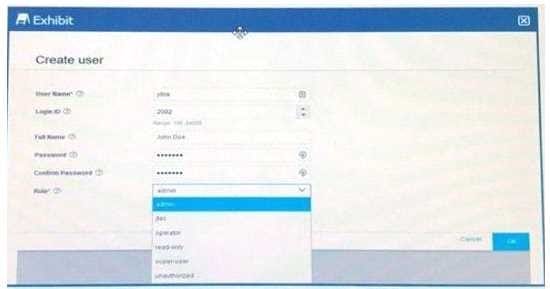
Which two user roles shown in the exhibit are available be defaults? (choose two)
A. Operator
B. Jtac
C. Super-user
D. Admin
Which Statement is correct about Sky ATP?
A. The local Sky ATP platform downloads the latest threat from managed site
B. Sky ATP can provide live threat feeds to SRX series devices
C. Sky ATP is a local hardware-based security threat analyzer that performs multiple tasks.
D. Sky ATP relies on the SRX series device to open and analyze suspect file attachments
Click the exhibit button
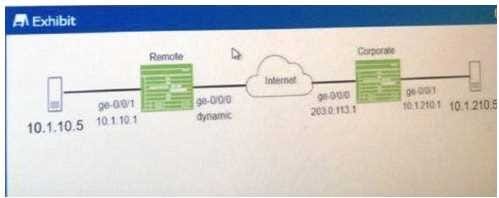
You are configuring an IPsec VPN for the network show in the exhibit Which feature must be enabled the VPN to established successfully?
A. Main mode must be configured on the IKE gateway
B. Main mode must be configured on the IPsec VPN
C. Aggressive mode must be configured on the IPsec VPN
D. Aggressive mode must be configured on IKE gateway

