JN0-210 Online Practice Questions and Answers
What are two virtualized components of a vMX? (Choose two)
A. VFP
B. vNIC
C. vSwitch
D. VCP
Juniper Networks SD-WAN feature is part of which product offering?
A. NorthStar
B. Cloud CPE solution
C. Sky ATP
D. Contrail Cloud
Click the Exhibit button. Exhibit:
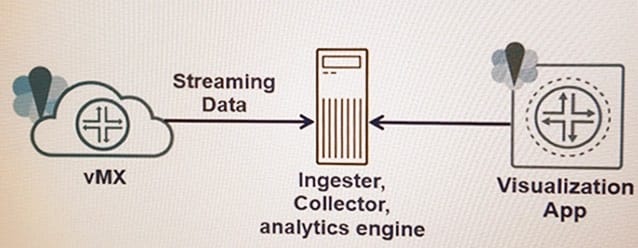
Which type of cloud system is shown in the exhibit?
A. cloud storage
B. cloud management
C. cloud telemetry
D. cloud security
Which SRX Series feature provides dynamic cloud-based malware analysis?
A. Sky ATP
B. identity management system
C. security policy
D. IPS policy
According to Juniper Networks, what are two recommended interior routing protocols for the underlay network? (Choose two)
A. IS-IS
B. RIP
C. OSPF
D. EIGRP
What is the Web interface component of OpenStack?
A. Horizon
B. Neutron
C. Nova
D. Cinder
What provisions new switches or routers in your network automatically, with no manual intervention?
A. PCEP
B. ZTP
C. BGP
D. RSVP
Which cloud architecture provides developers a framework on which to develop and customize applications?
A. DBaaS
B. PaaS
C. IaaS
D. FWaaS
What is used to provide secure access to a vSRX in a public cloud?
A. authorized key pairs
B. SSH key pairs
C. private key pairs
D. public key pairs

