HPE2-W05 Online Practice Questions and Answers
While troubleshooting integration between ClearPass and IntroSpect, you notice that there are no log events for either THROUGHPUT or ERROR in the ClearPass log source on the IntroSpect Analyzer. You are planning your troubleshooting actions.
Is this something you should check? (Check the authentication service being used in ClearPass for the Login - Logout enforcement policy.)
A. Yes
B. No
Refer to the exhibit.
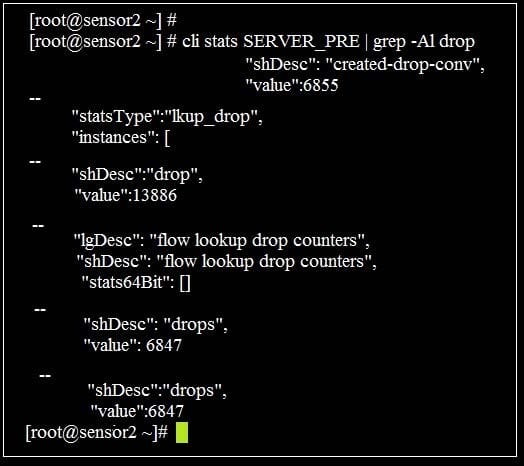
You are monitoring a new virtual packet processor with a network tap. You run the command "cli stats SERVER_PRE | gre-a1 drop" and then return an hour later and run the same command, but notice there is a significant increase in the number dropped packets.
Could this be a reason for the increase? (The Packet Processor may not be allocated the proper number of memory allocated on the VM server for the size of the TAP.)
A. Yes
B. No
You are one of the system administrators in your company, and you are assigned to monitor the IntroSpect system for alarms. Is this a correct statement about alarms? (The alarm bell icon on the header bar indicates active alarms, and clicking on it will take you to the Alerts>page.)
A. Yes
B. No
You are one of the system administrators in your company, and you are assigned to monitor the IntroSpect system for alarms. Is this a correct statement about alarms? (You must navigate to the IntroSpect Analyzer Menu>Alerts page to see if there are any alarms.)
A. Yes
B. No
In a meeting with a customer that runs a fully automated manufacturing facility that is connected to the business and corporate offices, the operations manager asks why they need IntroSpect to monitor the manufacturing network. Is this a reason they should monitor the manufacturing network security? (Because the controllers and sensors do not store customer data or corporate intellectual property, even if the automation network was to be breached it would not expose anything valuable.)
A. Yes
B. No
You deploy IntroSpect Analyzer in your existing network. You want to monitor email for suspect malware activity. Would this action be supported by IntroSpect? (Deploy a supported DNP like Proofpoint Email Protection, and integrate with The IntroSpect Analyzer.)
A. Yes
B. No
You are working on an IntroSpect Analyzer to fix an issue, and a restart is required after fixing the issue. Is this the correct procedure to restart? (From the Analyzer Menu navigate to Configuration ->System>Cluster Start/Stop->Restart Cluster.)
A. Yes
B. No
Refer to the exhibit.
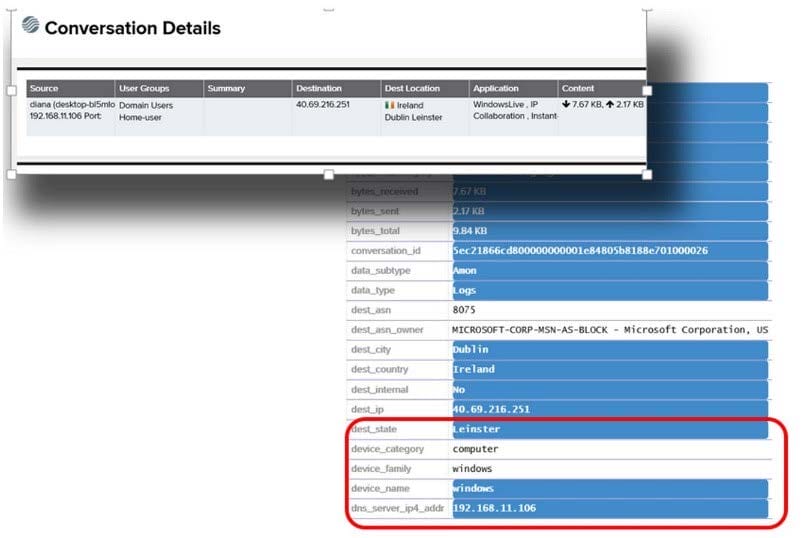
You are a security analyst for a company that has deployed an Aruba infrastructure, such as Mobility Controllers, ClearPass, and Airwave. Recently they have deployed Aruba IntroSpect for security analytics. You are looking at the conversation details of an entity. Is this statement correct about the details highlighted? (These details came from the ClearPass server and it has been integrated as a context server in the IntroSpect.)
A. Yes
B. No
You are visiting a site configured with IntroSpect, and the on-site admin tells you that they do not think that one of their database servers has fired any alerts for large download or strange access patterns. Could this be a reason? (The database server needs to be listed under Configuration>Analytics>User Correlation Config.)
A. Yes
B. No
While talking to an associate, they ask you to describe how different alerts in IntroSpect indicate compromise on the network. Would this be a correct statement? (If an entity executes a large download followed a few days later by a large upload to DropBox, this could be an indication that the entity is compromised.)
A. Yes
B. No

