HP2-W103 Online Practice Questions and Answers
Which challenges are enterprises and governments facing today?
A. The Cloud will fix all security issues; the only thing that matters will be the time to migrate.
B. Mobility is not user friendly in day-to-day life.
C. There are too many security experts available on the market. Hiring the best is extremely difficult.
D. the nature and motivation of attacks, transformation of enterprise IT and regulatory pressures
Which statement represents the vision of HP Fortify Software Security?
A. Assess > Fix > Protect
B. Assess > Assure > Report
C. Assess > Assure > Protect
D. Assess > Fix > Report
What is HP Fortify Software Security Center?
A. a flexible repository and reporting platform for security status, trending, and compliance
B. an onsite-only collaboration solution for reducing overhead of development teams
C. a native integration with ArcSight and TippingPoint for blocking and logging security activity events
D. an application built on the HP Anywhere platform for monitoring user server activities across networks, domains, and regions
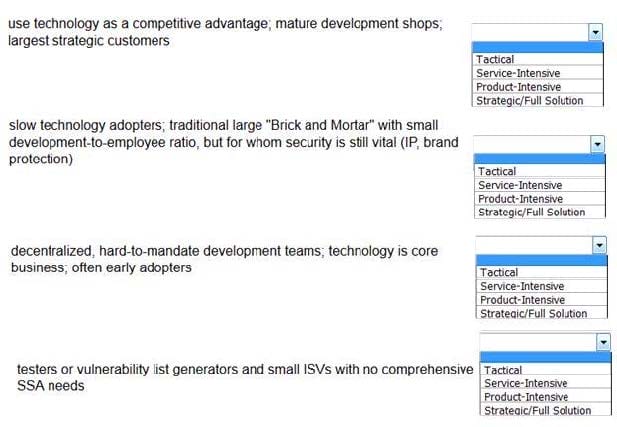
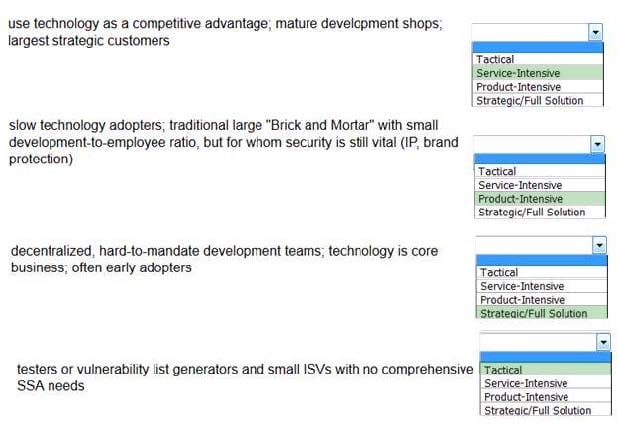
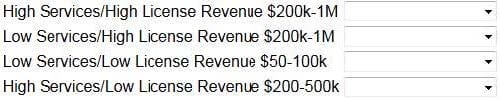
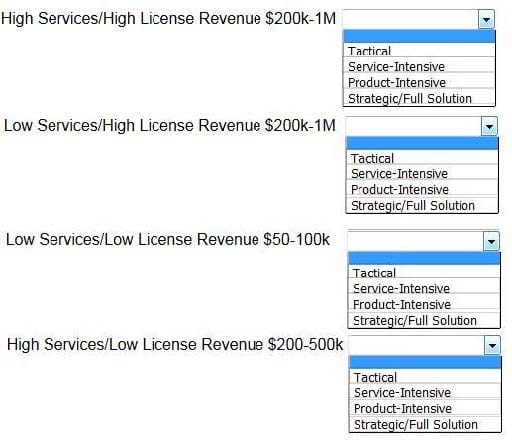
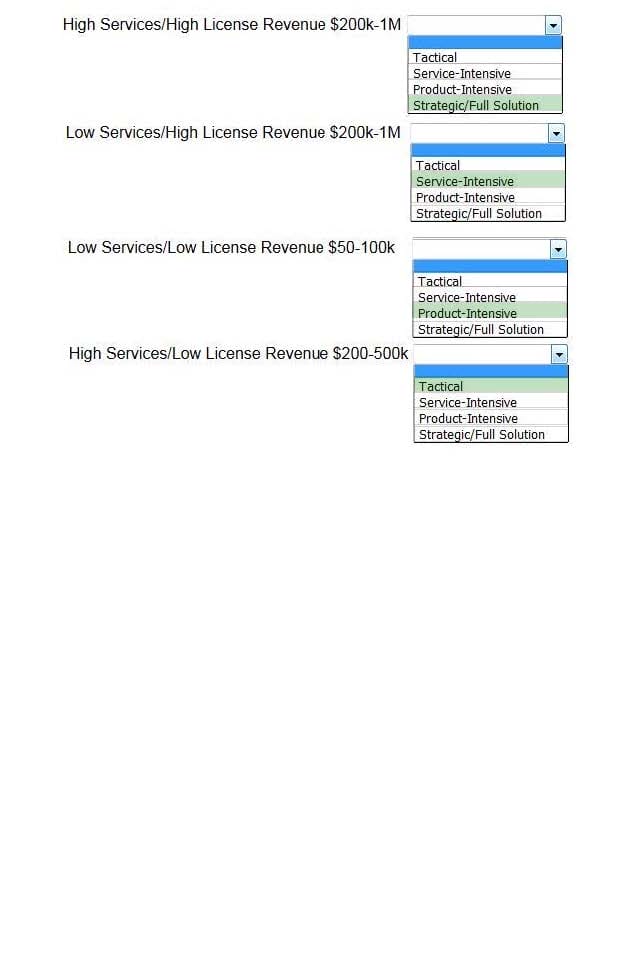
What are the main types of HP Fortify sales opportunities?
A. transactional opportunities and tactical opportunities
B. tactical opportunities and product-intensive opportunities
C. transactional opportunities and strategic enterprise solution opportunities
D. strategic enterprise solution opportunities and service-intensive opportunities
Which HP ESP pillar's solution detects and blocks attacks through the network?
A. HP TippingPoint
B. HP Fortify
C. HPArcSight
D. HP Atalla
What is the name given to modern cyber attacks that organizations face and fear the most?
A. APT or Advanced Persistent Threats
B. TPA or Total Penetrating Attacks
C. ATP or Attack Targeting Protocol
D. PTA or Parallel Threshold Attacks
What is the security approach that HP ESP adopted from Lockheed-Martin's Computer Emergency Response Team to disrupt the adversary?
A. the Kill Chain
B. the Destructor
C. the Internal Emergency Response Team
D. Detect it; Contain it, Stop it
Where should the bulk of the content appear in a proposal?
A. Scope
B. About
C. Proposal Overview
D. Problem Statement