H12-261 Online Practice Questions and Answers
The following is about the law of the China Security League Ipsec SA.
A. SA, SP (Security Parameter Index) IP is uniquely identified by a ternary group. This set of ternary includes security parameter prime, source address and usage. Security Number Agreement (or AH ESP)
B. Use the life to see the information about the encryption algorithm used by another display ipsec PSec, check the peer, etc. Interest traffic.
C. Only support encryption algorithm for data line encryption IPSec pair alignment.
D. IPSec SA Ipsec VPN pairs must be in two-way to establish
The description of the configuration is correct: (multiple BGP4+ selected)
A. Ruter-ID BGP4 Router-ID is the same as .
B. BGP4+ peer Link-Local specified when required
C. The next hop of the BGP4+ Link-Local route does not use an address.
D. BGP4+ BGP4 When the reflector is configured, the role of the reflector and the client needs to be the same as the configuration of the user.
E. BGP4+ does not support route reflectors.
The following description of cross-domain features is correct vpn Option C?
A. Reporting Forwarding Layer Labels Up to two are required in the script.
B. ASBR VPNV4, VPNv4 does not save routes, and does not advertise between routes.
C. VPN PE PE, the VPN route is exchanged between the ingress and the egress.
D. Cross-domain mode is not suitable when using multiple VPN-Option-c ASs.
On the network shown in the figure below, SW1, SW2 and SW3 are deployed. SW1 is the root bridge, link congestion occurs between SW1 and SW2, and SW2 cannot receive configuration BPDUs sent by the root bridge. Given this information, which of the following spanning tree protection mechanisms needs to be configured to prevent problems caused by link congestion?
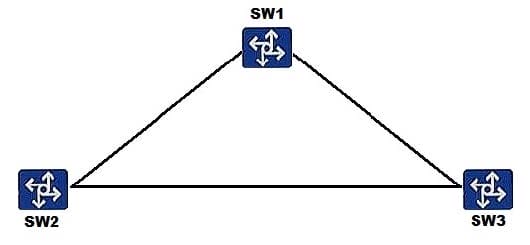
A. Defense against TC BPDU attacks
B. Root protection
C. BPDU protection
D. Loop protection
The figure shows router data. Which of the following statements is false?
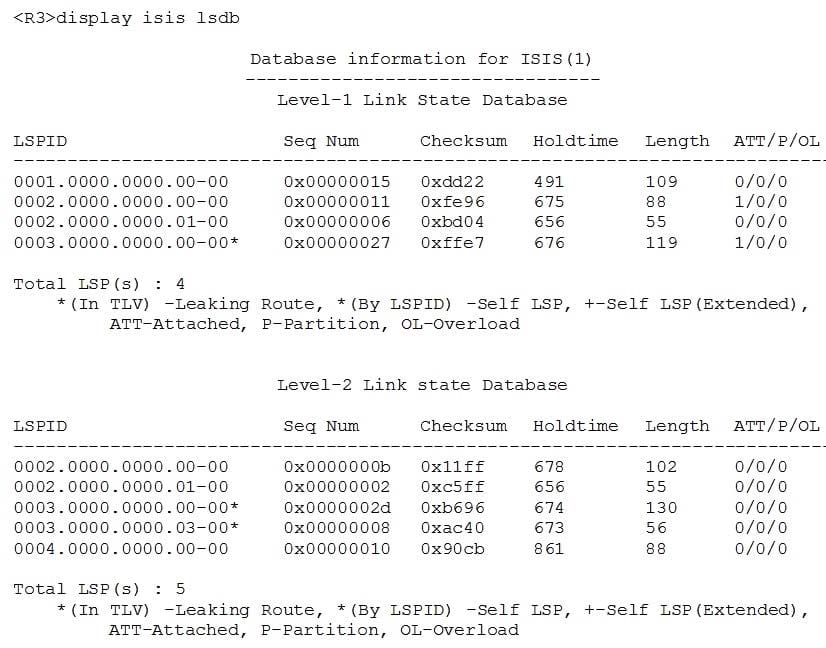
A. The system ID of R3 is 0003.0000.000
B. 3R is a Level-1-2 router.
C. R3 is the DlS of a Level-1 link.
D. R3 Is the DI5 of a level 2 link.
Assume that the traffic shaping rate is set to 100 Mbit/s on an interface and that the input bandwidth and PIR of each service are configured as shown in the table below.
What is the bandwidth allocated to the EF queue after the first round of scheduling?
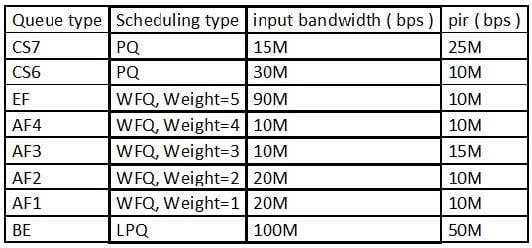
A. 30 Mbit/s
B. 90 Mbit/s
C. 25 Mbit/s
D. 15 Mbit/s
An AS-path-filter uses the regular expression ^[0-9]+$ to indicate all as-path attributes.
A. TRUE
B. FALSE
Which of the following lists, in the correct order, the protocols that use TCP ports 443, 179, 137, 110, and 23?
A. HTTPS, BGP, NetBios Name Server, POP3, Telnet
B. Finger, DHCP Server, NetBios Name Server, POP3, Telnet
C. BGP, POP3, SNMP, TFTP, Telnet
D. LDAP, SNMP, TFTP, POP3, Telnet
E. HTTPS, SNMP, POP3, DNS, Telnet
What are the possible causes for an establishment failure of an IBGP peer relationship between two routers?
A. Multi-hop IBGP is not configured.
B. There is no reachable IGP route between the routers.
C. Authentication fails.
D. The BGP protocol versions are different.
The configurations of two routers in a company are shown. Which of the following statements regarding the routing table of R1 is true?
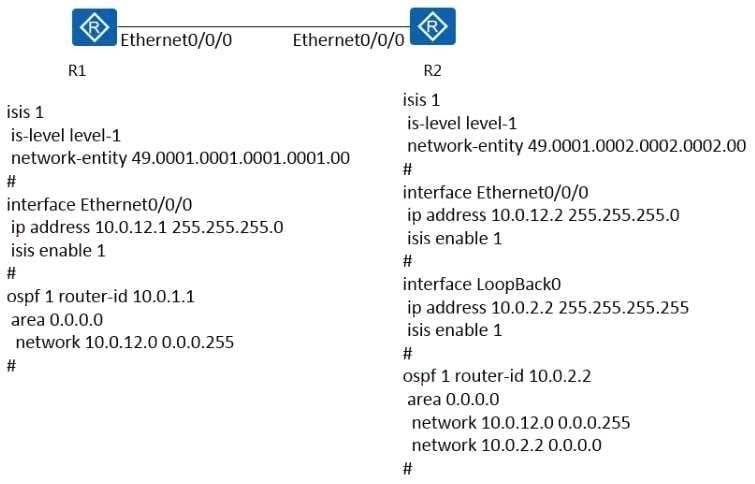
A. The IP routing entries whose destination network segment is 10.0.2.2/32 on R1 can be generated through OSPF only when the IS-IS preference of R2 is changed to 5
B. If the IS-IS preference of R1 is changed of R1 is changed to 5, the IP routing entries whose destination network segment is 10.0.2.2/32 on R1 are generated through OSPF
C. If the IS-IS preference of R1 is changed to 5, the IP routing entries whose destination network segment is 10.0.2.2/32 on R1 are generated through IS-IS
D. If the IS-IS preference of R2 is changed to 5, the IP routing entries whose destination network segment is 10.0.2.2/32 on R1 are generated through IS-IS

