GSEC Online Practice Questions and Answers
What is the first thing that should be done during the containment step of incident handling?
A. Change all the passwords
B. Secure the area
C. Prepare the Jump bag
D. Notify management
E. Prepare a report
When are Group Policy Objects (GPOs) NOT applied automatically to workstations?
A. At 90-minute intervals
B. At logon
C. Every time Windows Explorer is launched
D. At boot-up
Which of the following SIP methods is used to setup a new session and add a caller?
A. ACK
B. BYE
C. REGISTER
D. INVITE
E. CANCEL
Which of the following is the key point to consider in the recovery phase of incident handling?
A. Isolating the source of the compromise
B. Shutting down the system
C. Ensuring that vulnerable code is not being restored
D. Preparing the jump bag
How often is session information sent to the web server from the browser once the session information has been established?
A. With any change in session data
B. With every subsequent request
C. With any hidden form element data
D. With the initial request to register the session
Open the MATE terminal and use the tcpdump program to read - /pcaps /cass tech.pcap.
What is the source port number?
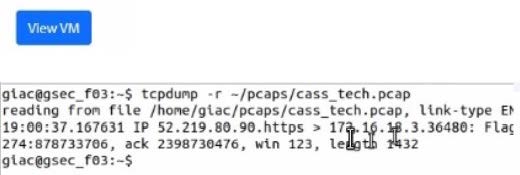
A. 878733706
B. 123
C. 443
D. 878732274
E. 36480
F. 2398730476
G. 1432
H. 80
I. 25
Which of the following is an advantage of private circuits versus VPNs?
A. Flexibility
B. Performance guarantees
C. Cost
D. Time required to implement
Which of the following files contains the shadowed password entries in Linux?
A. /etc/passwd
B. /etc/shadow
C. /etc/profile
D. /etc/shdpwd
An attacker gained physical access to an internal computer to access company proprietary data. The facility is protected by a fingerprint biometric system that records both failed and successful entry attempts. No failures were logged during the time periods of the recent breach. The account used when the attacker entered the facility shortly before each incident belongs to an employee who was out of the area. With respect to the biometric entry system, which of the following actions will help mitigate unauthorized physical access to the facility?
A. Try raising the Crossover Error Rate (CER)
B. Try to lower the False Accept Rate (FAR)
C. Try setting the Equal Error Rate (EER) to zero
D. Try to set a lower False Reject Rate (FRR)
What is TRUE about Workgroups and Domain Controllers?
A. By default all computers running Windows 2008 can only form Domain Controllers not Workgroups
B. Workgroups are characterized by higher costs while Domain Controllers by lower costs
C. You cannot have stand-alone computers in the midst of other machines that are members of a domain
D. Workgroup computers cannot share resources, only computers running on the same domain can
E. You can have stand-alone computers in the midst of other machines that are members of a domain.

