DES-1B31 Online Practice Questions and Answers
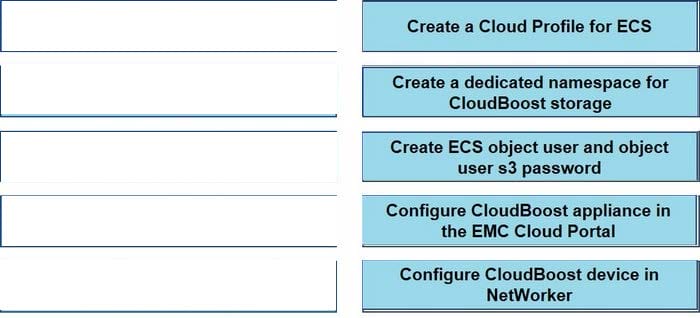
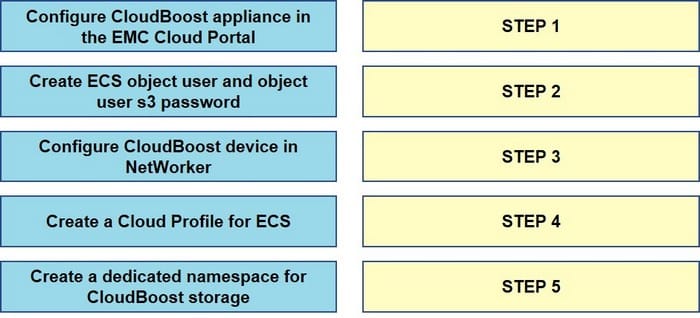
What is the correct sequence of steps to configure a NetWorker CloudBoost with ECS solution?
Select and Place:
Which data encryption mode is supported by ECS?
A. SEC 17-A4
B. Standard CBC
C. GCM
D. RSA BSAFE FIPS 140-2
An administrator has configured ECS to use NFSv3. What feature does this allow?
A. Global locking
B. Object storage access
C. Single protocol access
D. File gateway
Which configuration task is optional in ECS when enabling DD Cloud Tier integration?
A. Create a special bucket to store DD Cloud Tier objects
B. Create a dedicated namespace for DD Cloud Tier objects
C. Create an object user account for DD Cloud Tier objects
D. Create a dedicated storage pool for DD Cloud Tier objects
Which tab would a user select in the ECS portal to configure ESRS?
A. Settings
B. Manage
C. Dashboard
D. Connections
What is a correct statement concerning the use of ECS as an LTR solution with DD Cloud Tier?
A. Cloud units configured as a DD Cloud Tier can be ECS, public, or hybrid cloud
B. Data is moved directly from the active tier to ECS
C. Backups are cloned to the active tier via the app-based policy
D. Mission critical applications are backed up first to the DD Cloud Tier
A company is integrating Dell EMC Isilon CloudPools with the ECS and would like to enable CloudPools for disaster recovery failover. Which deep copy option should be used?
A. Force
B. Stub sync
C. Allow
D. Deny
On which level(s) is the ECS quota enforced?
A. Namespace only
B. Bucket only
C. Object user
D. Bucket and namespace
An ECS administrator creates a bucket to be used by the NFS clients. The development team tries to write some objects using the S3 browser on the bucket. They call the storage administrator to inform them that they are experiencing write operation errors.
What is a possible reason for the errors?
A. Bucket is Read only
B. Object user needs write credentials
C. Base URL was not configured
D. Secret key used is not correct
What technology is used in ECS to protect loss of a site in a two-site configuration?
A. Full Mirror Copy
B. Erasure Coding
C. XOR
D. Dual Parity