250-441 Online Practice Questions and Answers
What are two policy requirements for using the Isolate and Rejoin features in ATP? (Choose two.)
A. Add a Quarantine firewall policy for non-compliant and non-remediated computers.
B. Add a Quarantine LiveUpdate policy for non-compliant and non-remediated computers.
C. Add and assign an Application and Device Control policy in the Symantec Endpoint Protection Manager (SEPM).
D. Add and assign a Host Integrity policy in the Symantec Endpoint Protection Manager (SEPM).
E. Add a Quarantine Antivirus and Antispyware policy for non-compliant and non-remediated computers.
What does a Quarantine Firewall policy enable an ATP Administrator to do?
A. Isolate a computer while it is manually being remediated
B. Submit files to a Central Quarantine server
C. Filter all traffic leaving the network
D. Intercept all traffic entering the network
Which Advanced Threat Protection (ATP) component best isolates an infected computer from the network?
A. ATP: Email
B. ATP: Endpoint
C. ATP: Network
D. ATP: Roaming
Which stage of an Advanced Persistent Threat (APT) attack do attackers break into an organization's network to deliver targeted malware?
A. Incursion
B. Discovery
C. Capture
D. Exfiltration
What are the prerequisite products needed when deploying ATP: Endpoint, Network, and Email?
A. SEP and Symantec Messaging Gateway
B. SEP, Symantec Email Security.cloud, and Security Information and Event Management (SIEM)
C. SEP and Symantec Email Security.cloud
D. SEP, Symantec Messaging Gateway, and Symantec Email Security.cloud
In which scenario would it be beneficial for an organization to eradicate a threat from the environment by deleting it?
A. The Incident Response team is identifying the scope of the infection and is gathering a list of infected systems.
B. The Incident Response team is reviewing detections in the risk logs and assigning a High-Security Antivirus and Antispyware policy in the Symantec Endpoint Protection Manager (SEPM).
C. The Incident Response team completed their analysis of the threat and added it to a blacklist.
D. The Incident Response team is analyzing the file to determine if it is a threat or a false positive.
Which two non-Symantec methods for restricting traffic are available to the Incident Response team? (Choose two.)
A. Temporarily disconnect the local network from the internet.
B. Create an Access Control List at the router to deny traffic.
C. Analyze traffic using Wireshark protocol analyzer to identify the source of the infection.
D. Create a DNS sinkhole server to block malicious traffic.
E. Isolate computers so they are NOT compromised by infected computers.
Why is it important for an Incident Responder to copy malicious files to the ATP file store or create an image of the infected system during the Recovery phase?
A. To have a copy of the file policy enforcement
B. To test the effectiveness of the current assigned policy settings in the Symantec Endpoint Protection Manager (SEPM)
C. To create custom IPS signatures
D. To document and preserve any pieces of evidence associated with the incident
Which detection method identifies a file as malware after SEP has queried the file's reputation?
A. Skeptic
B. Vantage
C. Insight
D. Cynic
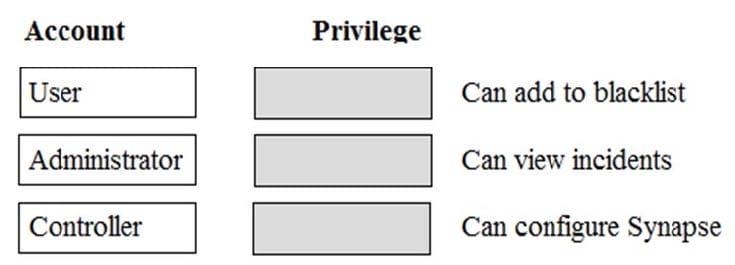
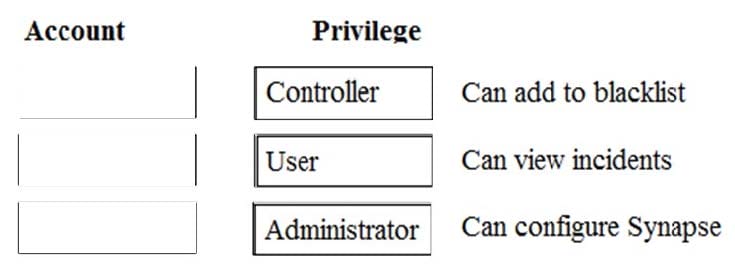
Which level of privilege corresponds to each ATP account type? Match the correct account type to the corresponding privileges.
Select and Place: