200-201 Online Practice Questions and Answers
What is the virtual address space for a Windows process?
A. physical location of an object in memory
B. set of pages that reside in the physical memory
C. system-level memory protection feature built into the operating system
D. set of virtual memory addresses that can be used
How does an SSL certificate impact security between the client and the server?
A. by enabling an authenticated channel between the client and the server
B. by creating an integrated channel between the client and the server
C. by enabling an authorized channel between the client and the server
D. by creating an encrypted channel between the client and the server
Which two components reduce the attack surface on an endpoint? (Choose two.)
A. secure boot
B. load balancing
C. increased audit log levels
D. restricting USB ports
E. full packet captures at the endpoint
Which data type is necessary to get information about source/destination ports?
A. statistical data
B. session data
C. connectivity data
D. alert data
What should a security analyst consider when comparing inline traffic interrogation with traffic tapping to determine which approach to use in the network?
A. Tapping interrogation replicates signals to a separate port for analyzing traffic
B. Tapping interrogations detect and block malicious traffic
C. Inline interrogation enables viewing a copy of traffic to ensure traffic is in compliance with security policies
D. Inline interrogation detects malicious traffic but does not block the traffic
Which statement describes patch management?
A. scanning servers and workstations for missing patches and vulnerabilities
B. process of appropriate distribution of system or software updates
C. managing and keeping previous patches lists documented for audit purposes
D. workflow of distributing mitigations of newly found vulnerabilities
Refer to exhibit.
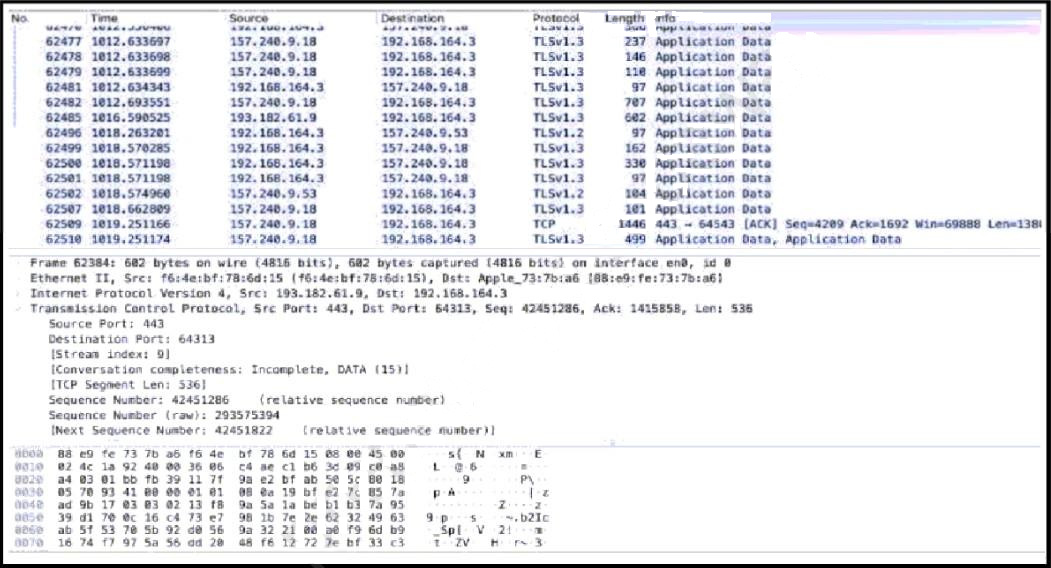
An analyst performs the analysis of the pcap file to detect the suspicious activity. What challenges did the analyst face in terms of data visibility?
A. data encapsulation
B. code obfuscation
C. data encryption
D. IP fragmentation
What is a description of "phishing" as a social engineering attack?
A. Fake Social Security Administration personnel contact random individuals, inform them that there has been a computer problem on their end, and ask that those individuals confirm their Social Security Number, all for the purpose of committing identity theft.
B. A hacker, masquerading as a trusted entity, dupes a victim into opening an email, instant message, or text message. The recipient is then tricked into clicking a malicious link.
C. The attacker focuses on creating a good pretext, or a fabricated scenario, that is used to try and steal victims
What is the impact of encryption on data visibility?
A. TLS 1.3 traffic cannot be decrypted and monitored.
B. Traffic decryption causes high CPU load on monitoring systems.
C. Traffic decryption is needed for deep inspection of SSL traffic via NGFW.
D. IPsec encryption of traffic is vulnerable to man-in-the-middle attacks.
What is the impact of encapsulation on the network?
A. Numerous local private addresses are mapped to a public one before the data is moved.
B. Something significant is concealed from virtually separate networks.
C. Web requests are taken on behalf of users and the response is collected from the web.
D. Logically separate functions in the network are abstracted from their underlying structures.

