1Z0-460 Online Practice Questions and Answers
Finding a directive issued by your organization listing several important CVEs (Common Vulnerability and Exposures), you find one for Linux OpenSSH (CVE-2006-5764), which might apply to your oracle Linux systems. What command would help ensure that a patch has been applied to close this vulnerability on an Oracle Linux 6 system running OpenSSH server?
A. yum listcves openssh
B. rpm qa | grep openssh | grep 5794
C. rpm q - - changelog openssh | grep 5794
D. yum sec list cves | grep 5794
E. yum sec list cvesApplied
What happens when the following command is run?
# authconfig - - passalgo = md5 - - update
A. It produces the MD5 checksum of the input data.
B. It configures the MD5 checksum for newly authored documents
C. It converts the stdio input to MD5 algorithm.
D. It changes the user password hashing algorithm to MD5.
Examine the sar command below. Your Oracle Linux system has one CPU. What does the runq- sz column of this output convey about your system?
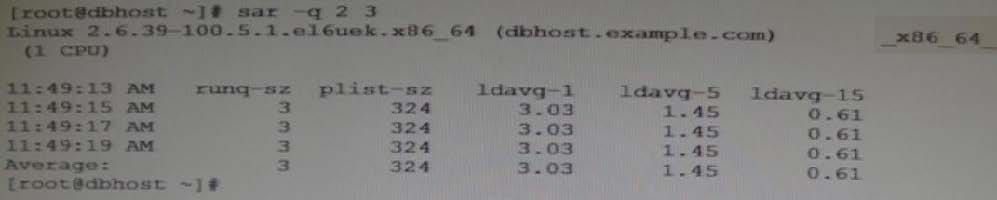
A. CPU is bottleneck because the run queue size is greater than the number of CPUs on your system.
B. The average of three processes are only using the CPU on your system and hence the CPU is not a bottleneck.
C. CPU is not a bottleneck because the run queue size indicates the number of CPU bound processes on your system.
D. CPU is a bottleneck because the run queue size indicates that adequate memory is not allocated.
Which two statements are correct about the Oracle ASMLib library?
A. Oracle ASMLib is an optional support library for the Automatic Storage Management (ASM) feature.
B. To use ASMLib library, you have to recompile it first for the Unbreakable Enterprise Kernel.
C. Oracle Automatic Storage management (ASM) requires Oracle ASMLib library to function completely.
D. Oracle ASMLib kernel driver is included in the Unbreakable Kernel.
You run the following command as the root user to set properties of a network interface (eth0):
# ifconfig eth0 192.0.2.102 netmask 255.255.255.0 up Setting network interface properties with the ifconfig utility is not persistent across system reboots. Which file would you edit to make settings and to make them persist across system reboots?
A. /etc/sysconfig/network file
B. /etc/sysconfig/network/ifcg-eth0 file
C. /etc/sysconfig/network-scripts/ifcfg-eth0 file
D. /etc/sysconfig/network-scripts/eth0 file
The ASMlib on Linux us designed to ___________.
A. Make managing ASM volume easier.
B. Make managing ASM volumes easier and provide a performance improvement over ASM volumes alone.
C. Provide load balancing across multiple volumes.
D. Allow the user to list contents of the volume from the OS command line.
The Oracle "helper" package (RPM), formerly known as "Oracle-validated" (which helps meet prerequisites for installing Oracle software), has been renamed. What is the new name?
A. Oracle-11gR2-validated
B. Oracle-11fR2-valid_package
C. Oracle-rdbms-server-11gR2-preinstall
D. Oracle-11gR2-preinstall
View the exhibit.
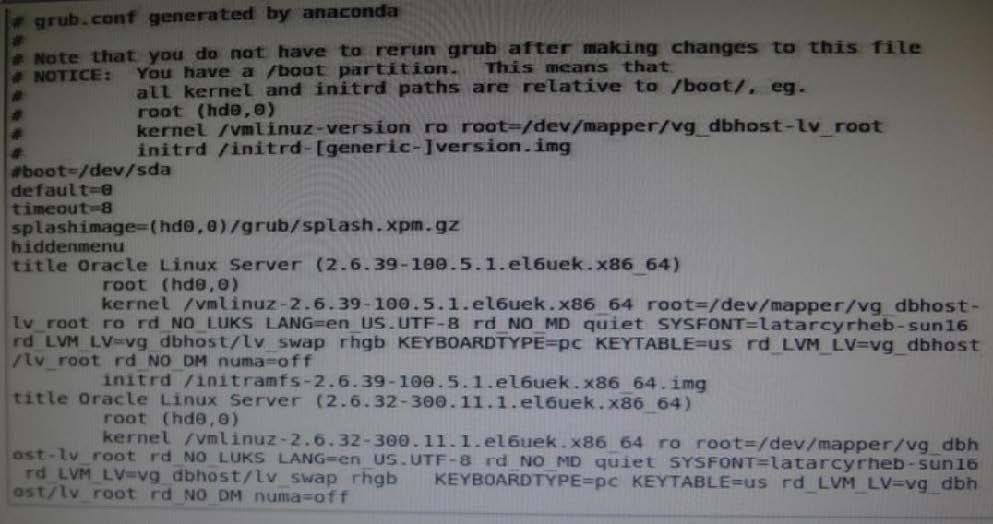
Examine the grub.conf file snippet in the Exhibit. Which statement is true if your Linux system boots by using this grub.conf file?
A. GRUB will boot, by default, the first kernel entry of this grub.conf file.
B. GRUB will prompt you to select the kernel to be booted because the default parameter is set to 0.
C. GRUB will boot the kernel specified in the inittab file of the system.
D. GRUB will boot, by default, the second kernel entry of this grub.conf file.
You want to add a README.txt file in the home directory of every new user that you create by using the useradd command on your Oracle Linux system. In which directory will you place the README.txt file so that it automatically gets copied to the new user's home directory when the user is created?
A. /home/users
B. /etc/default/useradd
C. /etc/default
D. /etc/skel
Which two statements are true about Oracle Clusterware Software?
A. Oracle Clusterware is a portable software that allows clustering of single servers so that they cooperate as single system.
B. Oracle Clusterware is a portable cluster software that can be installed on Oracle Engineered Systems.
C. Oracle Linux Support customers at the Basic or premier level are entitled, at no additional license and support costs, to download and deploy Oracle Clusterware in Linux cluster covered their Linux Support agreement.
D. Oracle Clusterware is an add-on software that is supported Oracle Linux only.

