1Z0-1084-22 Online Practice Questions and Answers
Which is NOT a valid option to execute a function deployed on Oracle Functions?
A. Send a signed HTTP requests to the function's invoke endpoint
B. Invoke from Oracle Cloud Infrastructure CLI
C. Invoke from Docker CLI
D. Trigger by an event in Oracle Cloud Infrastructure Events service
E. Invoke from Fn Project CLI
How do you perform a rolling update in Kubernetes?
A. kubect1 rolling-update
B. kubect1 upgrade
C. kubect1 update -c
D. kubect1 rolling-update
Which two "Action Type" options are NOT available in an Oracle Cloud Infrastructure (OCI) Events rule definition?
A. Notifications
B. Functions
C. Streaming
D. Email
E. Slack
Which statements is incorrect with regards to the Oracle Cloud Infrastructure (OCI) Notifications service?
A. Notification topics may be assigned as the action performed by an OCI Events configuration.
B. OCI Alarms can be configured to publish to a notification topic when triggered.
C. An OCI function may subscribe to a notification topic.
D. A subscription can forward notifications to an HTTPS endpoint.
E. A subscription can integrate with PagerDuty events.
F. It may be used to receive an email each time an OCI Autonomous Database backup is completed.
How can you find details of the tolerations field for the sample YAML file below?
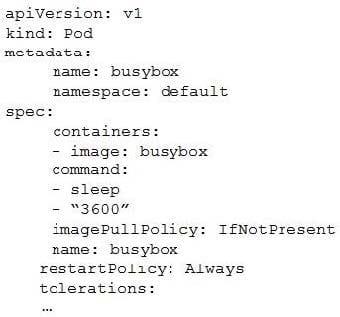
A. kubectl list pod.spec.tolerations
B. kubectl explain pod.spec.tolerations
C. kubectl describe pod.spec tolerations
D. kubectl get pod.spec.tolerations
Your organization uses a federated identity provider to login to your Oracle Cloud Infrastructure (OCI) environment. As a developer, you are writing a script to automate some operation and want to use OCI CLI to do that. Your security team
doesn't allow storing private keys on local machines.
How can you authenticate with OCI CLI?
A. Run oci setup keys and provide your credentials
B. Run oci session refresh --profile
C. Run oci session authenticate and provide your credentials
D. Run oci setup oci-cli-rc --file path/to/target/file
Which header is NOT required when signing GET requests to Oracle Cloud Infrastructure APIs?
A. date or x-date
B. (request-target)
C. content-type
D. host
You have deployed a Python application on Oracle Cloud Infrastructure Container Engine for Kubernetes. However, during testing you found a bug that you rectified and created a new Docker image. You need to make sure that if this new
Image doesn't work then you can roll back to the previous version.
Using kubectl, which deployment strategies should you choose?
A. Rolling Update
B. Canary Deployment
C. Blue/Green Deployment
D. A/B Testing
What is the difference between blue/green and canary deployment strategies?
A. In blue/green, application Is deployed In minor increments to a select group of people. In canary, both old and new applications are simultaneously in production.
B. In blue/green, both old and new applications are in production at the same time. In canary, application is deployed Incrementally to a select group of people.
C. In blue/green, current applications are slowly replaced with new ones. In < MW y, Application ll deployed incrementally to a select group of people.
D. In blue/green, current applications are slowly replaced with new ones. In canary, both old and new applications are In production at the same time.
Which two statements accurately describe Oracle SQL Developer Web on Oracle Cloud Infrastructure (OCI) Autonomous Database?
A. It is available for databases with dedicated Exadata infrastructure only.
B. After provisioning into an OCI compute Instance, it can automatically connect to the OCI Autonomous Databases instances.
C. It is available for databases with both dedicated and shared Exadata infrastructure.
D. It provides a development environment and a data modeler interface for OCI Autonomous Databases.
E. It must be enabled via OCI Identity and Access Management policy to get access to the Autonomous Databases instances.

