1Y0-340 Online Practice Questions and Answers
A Citrix Engineer has deployed Front-end Optimization on NetScaler. The following are the snippets of the content before and after optimization.
Before Optimization: Which optimization technique has been applied to the content?
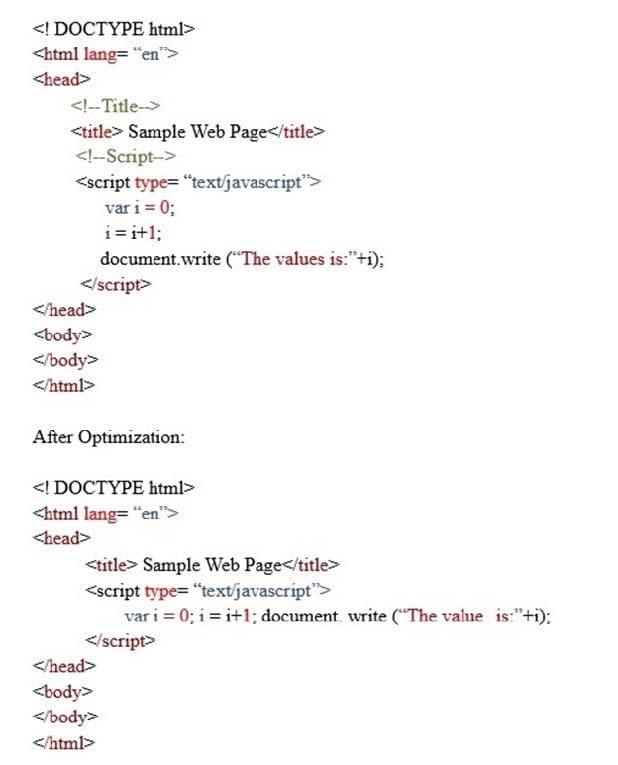
A. Convert linked JavaScript to inline JavaScript
B. Minify JavaScript
C. Move JavaScript to End of Body Tag
D. Inline JavaScript
A Citrix Engineer is configuring an Application Firewall Policy to protect a website. Which expression will the engineer use in the policy?
A. HTTP.RES.IS_VALID
B. HTTP.REQ.HOSTNAME.EQ ("true")
C. HTTP.RES.HEADER ("hostname").EQ ("true")
D. HTTP.REQ.IS_VALID
A Citrix Engineer observes that when the application firewall policy is bound to the virtual server, some of the webpages are NOT loading correctly.
Which log file can the engineer use to view the application firewall-related logs in the native format?
A. /var/log/iprep.log
B. /var/nslog/newnslog
C. /var/nslog/ns.log
D. /var/log/ns.log
Scenario: A Citrix Engineer has migrated an application to NetScaler to secure it from application layer attacks. The engineer receives a complaint that the application is timing out while users are actively accessing the page. Those users are forced to reestablish the connection.
What can be the cause of this issue?
A. The maximum session lifetime is NOT configured.
B. The session time out is configured to a low value.
C. The application is configured with a low session timeout.
D. The maximum session lifetime is less than the session timeout.
Scenario: A Citrix Engineer has configured LDAP group extraction on the NetScaler Management and Analytics System (NMAS) for the administration. The engineer observes that extraction is NOT working for one of the five configured groups.
What could be the cause of the issue?
A. The admin bind user has read-only permissions on the LDAP server.
B. The NMAS group does NOT match the one on the external LDAP servers.
C. The LDAP bind DN is incorrectly configured in the LDAP profile.
D. The user group extraction is NOT supported with plaintext LDAP.
Scenario: A Citrix Engineer has deployed Front-end Optimization on NetScaler. Below is the snippet of the content before and after optimization.
Before Optimization:
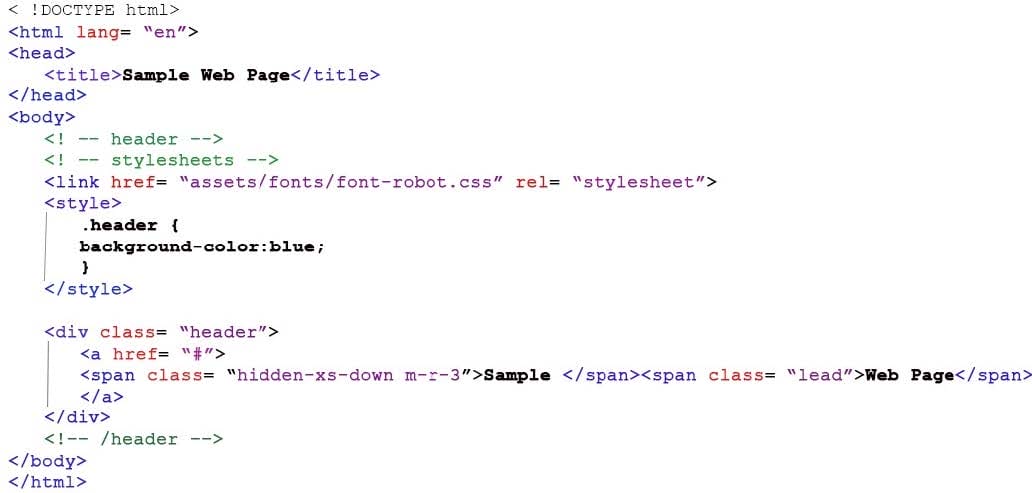
After Optimization:
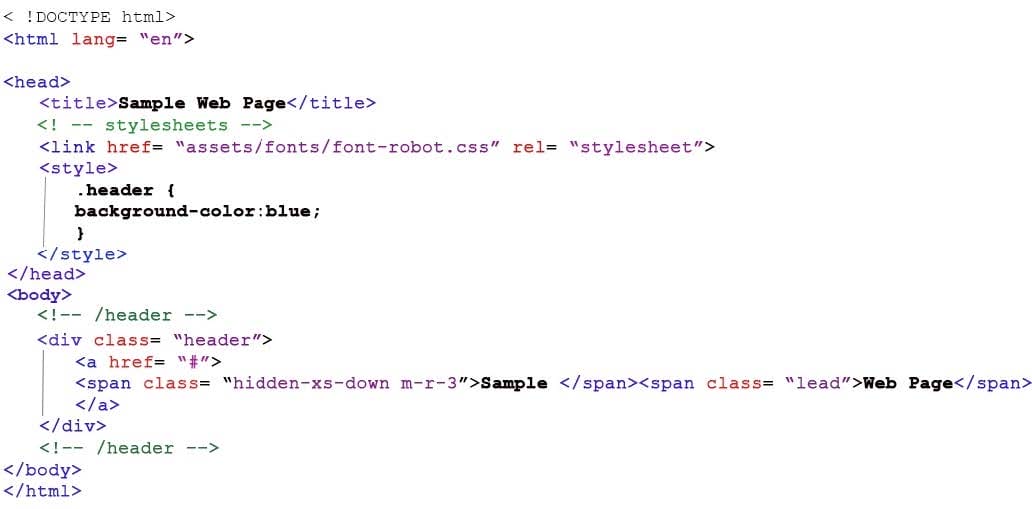
Which optimization technique has been applied to the content?
A. CSS Minify
B. CSS Combine
C. CSS Move to Head Tag
D. CSS Make Inline
A Citrix Engineer enabled Credit Card Security check in the Application Firewall Profile. Which response header will be dropped by Application Firewall after this check is enabled?
A. Content-Encoding
B. Content-Location
C. Content-Type
D. Content-Length
Which Markup Language is used along with NITRO API to create a StyleBook?
A. YAML
B. GML
C. XML
D. HTML
A Citrix Engineer needs to configure NetScaler Management and Analytics System (NMAS) in their network to retain network reporting data, events, audit logs, and task logs for 20 days.
Which settings can the engineer configure to meet the requirement?
A. System Prune Settings
B. System Backup Settings
C. Instance Backup Settings
D. Syslog Prune Settings
Scenario: A Citrix Engineer has enabled Security insight and Web insight on NetScaler Management and Analytics System (NMAS). The engineer is NOT able to see data under the Analytics on NMAS, in spite of
seeing hits on the APPFLOW policy.
Which log should the engineer check on NMAS to ensure that the information is sent from NetScaler?
A. mps_afanalytics.log
B. mps_perf.log
C. mps_afdecoder.log
D. nstriton.log

