1D0-571 Online Practice Questions and Answers
You have discovered that the ls, su and ps commands no longer function as expected. They do not return information in a manner similar to any other Linux system. Also, the implementation of Tripwire you have installed on this server is returning new hash values. Which of the following has most likely occurred?
A. Atrojan has attacked the system.
B. A SQL injection attack has occurred.
C. A spyware application has been installed. D. A root kit has been installed on the system.
You are using a PKI solution that is based on Secure Sockets Layer (SSL). Which of the following describes the function of the asymmetric-key-encryption algorithm used?
A. It encrypts the symmetric key.
B. It encrypts all of the data.
C. It encrypts the hash code used for data integrity.
D. It encrypts the X.509 key.
Which of the following is a typical target of a trojan on a Linux system?
A. Kernel modules
B. Shared libraries
C. Boot sector files
D. System32 DLL files
You want to create a quick solution that allows you to obtain real-time login information for the administrative account on an LDAP server that you feel may become a target. Which of the following will accomplish this goal?
A. Reinstall the LDAP service on the server so that it is updated and more secure.
B. Install an application that creates checksums of the contents on the hard disk.
C. Create a login script for the administrative account that records logins to a separate server.
D. Create a dummy administrator account on the system so that a potential hacker is distracted from the
real login account.
Which of the following is the primary weakness of symmetric-key encryption?
A. Data encrypted using symmetric-key encryption is subject to corruption during transport.
B. Symmetric-key encryption operates slower than asymmetric-key encryption.
C. Symmetric-key encryption does not provide the service of data confidentiality.
D. Keys created using symmetric-key encryption are difficult to distribute securely.
Which of the following is a common problem, yet commonly overlooked, in regards to physical security in server rooms?
A. Firewalls that do not have a dedicated backup
B. False ceilings
C. Logic bombs
D. Biometric malfunctions
Which tool is best suited for identifying applications and code on a Web server that can lead to a SQL injection attack?
A. A vulnerability scanner
B. A packet sniffer
C. An intrusion-detection system
D. A network switch
Which of the following is a primary auditing activity?
A. Encrypting data files
B. Changing login accounts
C. Checking log files
D. Configuring the firewall
Consider the following diagram involving two firewall-protected networks: Which of the following is necessary for each of the firewalls to allow private IP addresses to be passed on to the Internet?
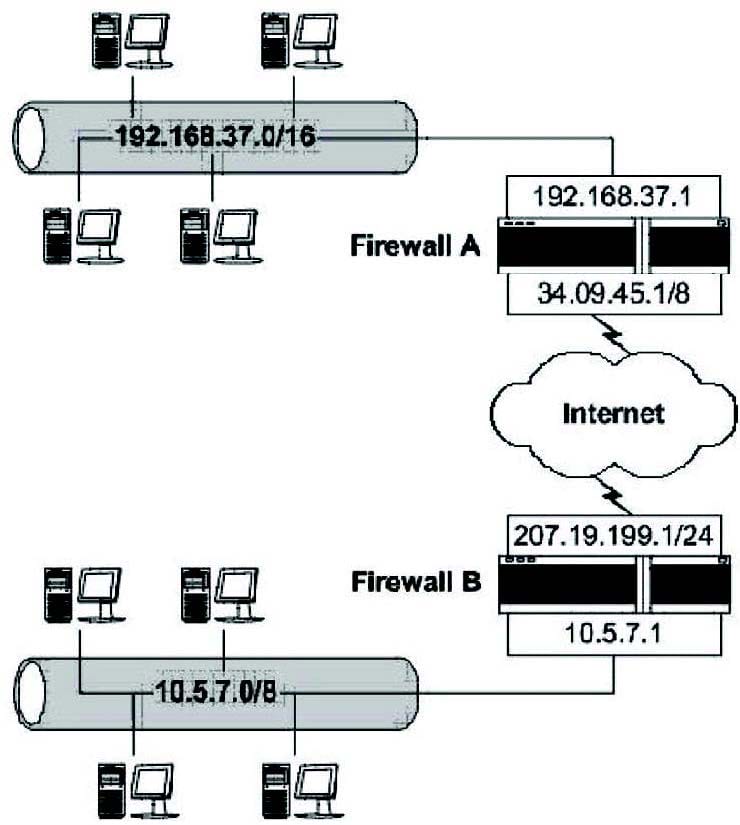
A. Chargeback
B. Stateful multi-layer inspection
C. Masquerading
D. DMZ creation
What is the primary strength of symmetric-key encryption?
A. It allows easy and secure exchange of the secret key.
B. It creates aash?of a text, enabling data integrity.It creates a ?ash?of a text, enabling data integrity.
C. It can encrypt large amounts of data very quickly.
D. It provides non-repudiation services more efficiently than asymmetric-key encryption.

