101 Online Practice Questions and Answers
CORRECT TEXT The layer 3 security feature _______ Cookies that protects against SYN floods, DoS, and DDoS attacks. (Fill in)
When using a single BIG-IP with APM, an organization can support up to 60,000 concurrent remote access users.
A. True
B. False
Why would an administrator capture monitor traffic between a BIG-IP and servers?
A. Viewing monitor traffic could help the administrator to define a more robust monitor.
B. If a client were having difficulty logging into a load balanced SSH server, viewing and analyzing the connection process would determine the reason.
C. Only client traffic may be captured; monitor traffic may not be captured.
D. If client traffic to servers was failing, viewing and analyzing monitor traffic would determine the reason.
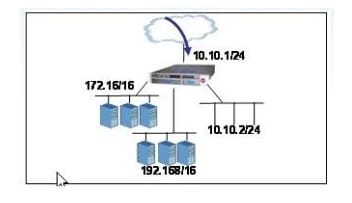
An LTM has the 3 virtual servers, four self IP addresses defined and the networks shown in the exhibit. Selected options for each object are shown below. Settings not shown are at their defaults.
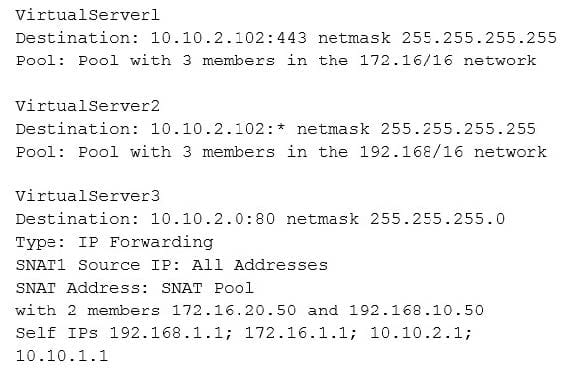
A connection attempt is made with a source IP and port of 10.20.100.50:2222 and a destination IP and port of 10.10.2.102:80. When the request is processed, what will be the destination IP address?
A. Destination IP: 10.10.2.102
B. The request will be dropped.
C. Destination IP: pool member in the 192.168/16 network
D. Destination IP: pool member in the 172.16/16 network
Which VLANs must be enabled for a SNAT to perform as desired (translating only desired packets)?
A. The SNAT must be enabled for all VLANs.
B. The SNAT must be enabled for the VLANs where desired packets leave the BIG-IP.
C. The SNAT must be enabled for the VLANs where desired packets arrive on the BIG-IP.
D. The SNAT must be enabled for the VLANs where desired packets arrive and leave the BIG-IP.
Tightening is a feature of which type of entity?
A. Explicit URLs
B. Attack signatures
C. Flow login URLs
D. Wildcard parameters
A BIG-IP Administrator is trying to send traffic to a server on the same subnet and sees an incomplete in the BIG-IP devices ARP table. What could cause the incomplete status?
A. BIG-IP device connection is half-duplex
B. Router does not have a default gateway
C. Firewall is blocking ICMP
D. Server's switch connection is in the wrong VLAN
What are three functions commonly performed by HTTP cookies? (Choose three)
A. Track users' browsing activities
B. hold User preferences
C. maintain session state
D. execute client side scripts
E. execute server side scripts
Which command should a BIG-IP Administrator use to resolve the domain www. F5.com?
A. grep
B. ping
C. dig
D. find
A BIG-IP Administrator configures three Network Time Protocol servers to keep the time of the devices in sync.
Which tool should the administrator use to show the synchronization status with the Network Time Protocol servers ?
A. ntpdate
B. time
C. mpa
D. date

