117-202 Online Practice Questions and Answers
What command must be used to create an SSH key-pair? Please enter the command without the path or any options or parameters.
The following data is some of the output produced by a program. Which program produced this output?
strftime (" Thu", 1024, "%a", 0xb7f64380) =4 fwrite ("Thu", 3, 1, 0xb7f614e0) =1 fputc (' ', 0xb7f614e0) =32 strftime (" Feb", 1024, " %b", 0xb7f64380) =4 fwrite ("Feb", 3, 1, 0xb7f614e0) =1 fputc (' ', 0xb7f614e0) =32 fwrite ("19", 2, 1, 0xb7f614e0) =1
A. lsof
B. ltrace
C. nm
D. strace
E. time
What is the name of the network security scanner project which, at the core, is a server with a set of network vulnerability tests (NVTs)?
A. nmap
B. OpenVAS
C. Snort
D. wireshark
Which option is used to configure pppd to use up to two DNS server addresses provided by the remote server?
A. ms-dns
B. nameserver
C. usepeerdns
D. dns
E. None of the above
The Internet gateway connects the clients with the Internet by using a Squid proxy. Only the clients from the network 192.168.1.0/24 should be able to use the proxy. Which of the following configuration sections is correct?
A. acl local src 192.168.1.0/24 http_allow local
B. acl local src 192.168.1.0/24 http_access allow local
C. acl local src 192.168.1.0/24 http access allow local
D. acl local src 192.168.1.0/24 http_access_allow=local
E. acl local src 192.168.1.0/24 httpd local allow
The internal network (192.168.1.0-192.168.1.255) needs to be able to relay email through the site's sendmail server. What line must be added to /etc/mail/access to allow this?
A. 192.168.1.0/24 RELAY
B. 192.168.1 RELAY
C. 192.168.1.0/24 OK
D. 192.168.1 OK
The command route shows the following output:
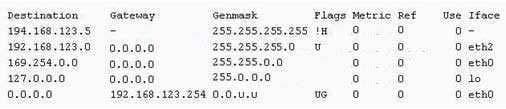
Which of the following statements is correct?
A. The network 169.254.0.0 is not a valid route.
B. The host 194.168.123.5 is temporarily down.
C. The host route 194.168.123.5 is rejected by the kernel.
D. The "!H " signals that traffic to the host 194.168.123.5 is dropped.
E. The network path to the host 194.168.123.5 is not available.
For what purpose is TCP/IP stack fingerprinting used by nmap?
A. It is used to determine the remote operating system.
B. It is used to filter out responses from specific servers.
C. It is used to identify duplicate responses from the same remote server.
D. It is used to masquerade the responses of remote servers.
E. It is used to uniquely identify servers on the network for forensics.
What option for BIND is required in the global options to disable recursive queries on the DNS server by default?
A. allow-recursive-query { none; };
B. allow-recursive-query off;
C. recursion { none; };
D. recursion no;

