210-255 Online Practice Questions and Answers
Which two components are included in a 5-tuple? (Choose two.)
A. port number
B. destination IP address
C. data packet
D. user name
E. host logs
Refer to the Exhibit. A customer reports that they cannot access your organization's website. Which option is a possible reason that the customer cannot access the website?
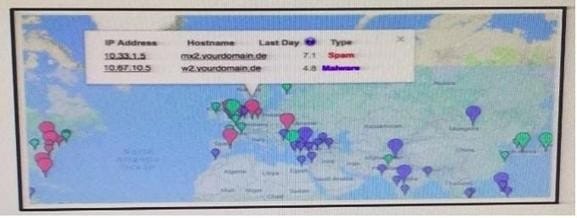
A. The server at 10.33.1.5 is using up too much bandwidth causing a denial- of-service.
B. The server at 10.67.10.5 has a virus.
C. A vulnerability scanner has shown that 10.67.10.5 has been compromised.
D. Web traffic sent from 10.67.10.5 has been identified as malicious by Internet sensors.
Which Security Operations Center's goal is to provide incident handling to a country?
A. Coordination Center
B. Internal CSIRT
C. National CSIRT
D. Analysis Center
Which of the following steps in the kill chain would come before the others?
A. C2
B. Delivery
C. Installation
D. Exploitation
Refer to exhibit. Which option is the logical source device for these events?
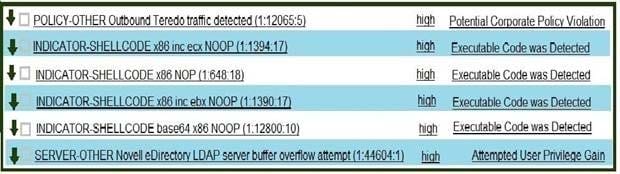
A. web server
B. NetFlow collector
C. proxy server
D. IDS/IPS
What is a common artifact used to uniquely identify a detected file?
A. file size
B. file extension
C. file timestamp
D. file hash
Which signature type results in a legitime alert been dismissed?
A. True negative
B. False negative
C. True Positive
D. False Positive
What can be addressed when using retrospective security techniques?
A. if the affected host needs a software update
B. what system are affected
C. if the affected system needs replacement
D. why the malware is still in our network
Which of the following file systems is more secure, scalable, and advanced?
A. FAT32
B. FAT64
C. uFAT
D. NTFS
Which expression allows you to filter on network numbers?
A. ether [src|dst] host
B. gateway host
C. [src|dst] net
D. [tcp|udp] [src|dst] port

