AZ-500 Online Practice Questions and Answers
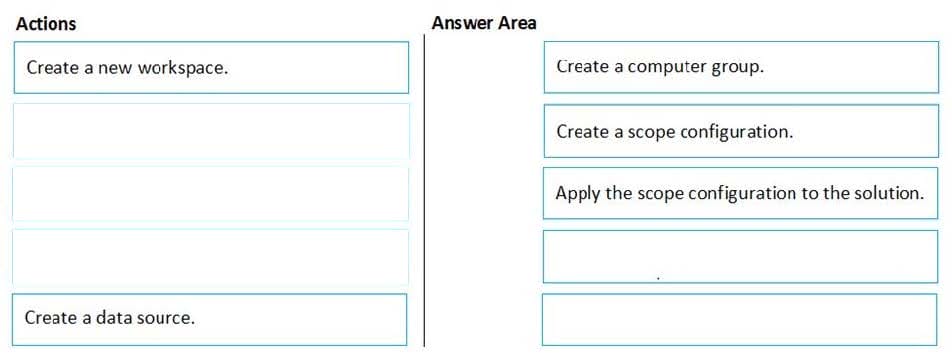
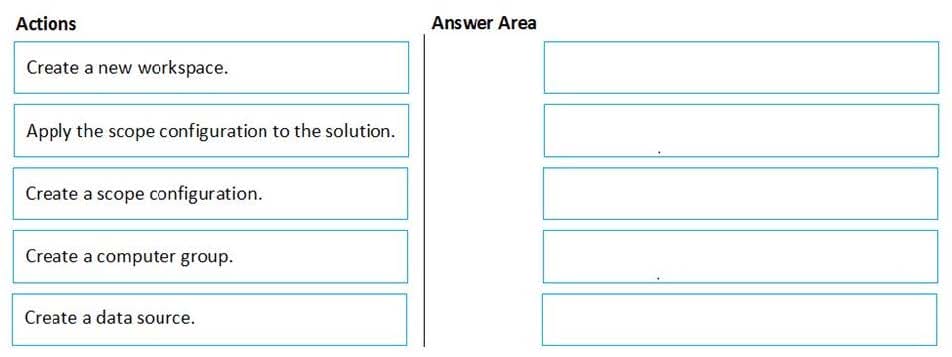
DRAG DROP
You have an Azure subscription named Sub1 that contains an Azure Log Analytics workspace named LAW1.
You have 500 Azure virtual machines that run Windows Server 2016 and are enrolled in LAW1.
You plan to add the System Update Assessment solution to LAW1.
You need to ensure that System Update Assessment-related logs are uploaded to LAW1 from 100 of the virtual machines only.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
Select and Place:
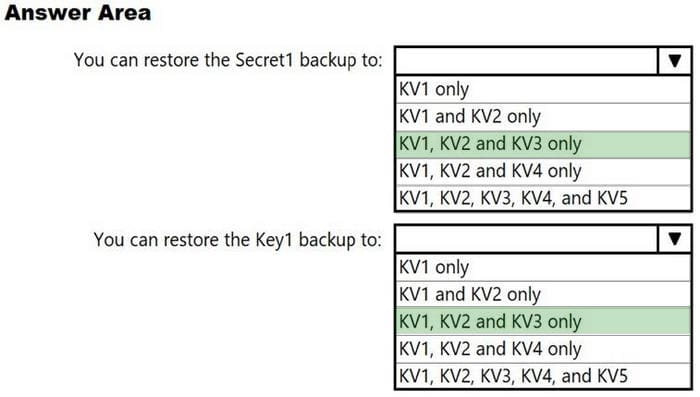
HOTSPOT
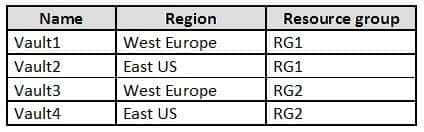
You have the Azure key vaults shown in the following table.
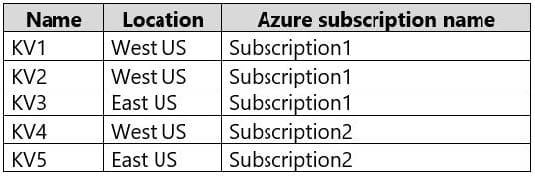
KV1 stores a secret named Secret1 and a key for a managed storage account named Key1.
You back up Secret1 and Key1.
To which key vaults can you restore each backup? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area:
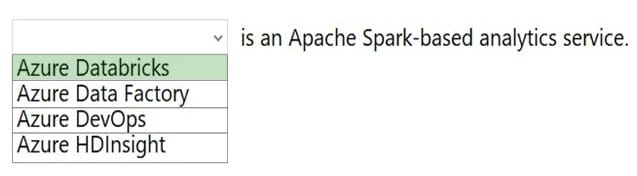
HOTSPOT
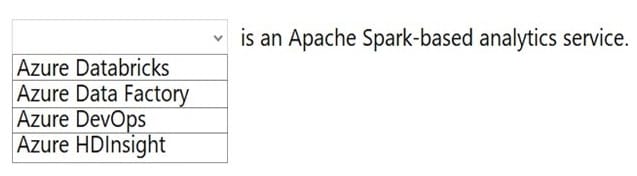
To complete the sentence, select the appropriate option in the answer area.
Hot Area:
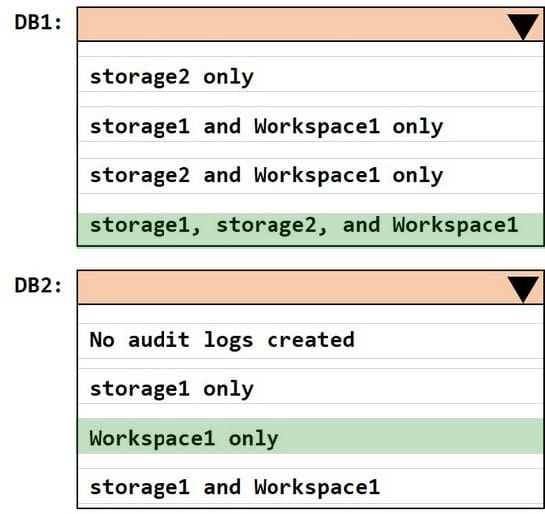
HOTSPOT - (Topic 4)
You have an Azure subscription that contains the resources shown in the following table.
Pass Your Certification With Marks4sure Guarantee 398 Microsoft AZ-500 : Practice Test
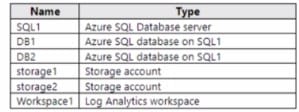
SQL1 has the following configurations:
1.
Auditing: Enabled
2.
Audit log destination: storage1, Workspace1
DB1 has the following configurations:
1.
Auditing: Enabled
2.
Audit log destination: storage2
DB2 has auditing disabled.
Where are the audit logs for DB1 and DB2 stored?
To answer, select the appropriate options in the answer area
NOTE: Each correct selection is worth one point.
Hot Area:
SIMULATION
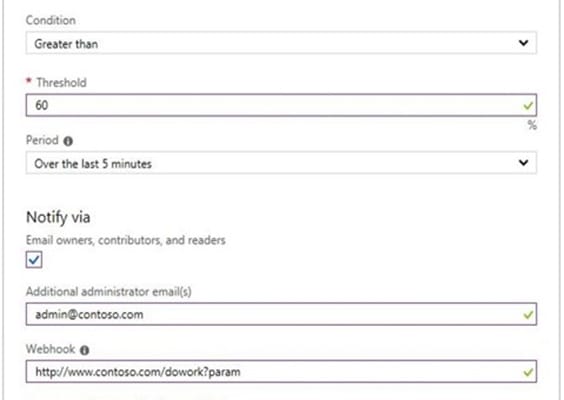
You need to email an alert to a user named [email protected] if the average CPU usage of a virtual machine named VM1 is greater than 70 percent for a period of 15 minutes.
To complete this task, sign in to the Azure portal.
A. See the explanation below.
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while
others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have an Azure Subscription named Sub1.
You have an Azure Storage account named Sa1 in a resource group named RG1.
Users and applications access the blob service and the file service in Sa1 by using several shared access signatures (SASs) and stored access policies.
You discover that unauthorized users accessed both the file service and the blob service.
You need to revoke all access to Sa1.
Solution: You generate new SASs.
Does this meet the goal?
A. Yes
B. No
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while
others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a hybrid configuration of Azure Active Directory (Azure AD).
You have an Azure HDInsight cluster on a virtual network.
You plan to allow users to authenticate to the cluster by using their on-premises Active Directory credentials.
You need to configure the environment to support the planned authentication.
Solution: You deploy an Azure AD Application Proxy.
Does this meet the goal?
A. Yes
B. No
You plan to deploy Azure container instances.
You have a containerized application that validates credit cards. The application is comprised of two containers: an application container and a validation container.
The application container is monitored by the validation container. The validation container performs security checks by making requests to the application container and waiting for responses after every transaction.
You need to ensure that the application container and the validation container are scheduled to be deployed together. The containers must communicate to each other only on ports that are not externally exposed.
What should you include in the deployment?
A. application security groups
B. network security groups (NSGs)
C. management groups
D. container groups
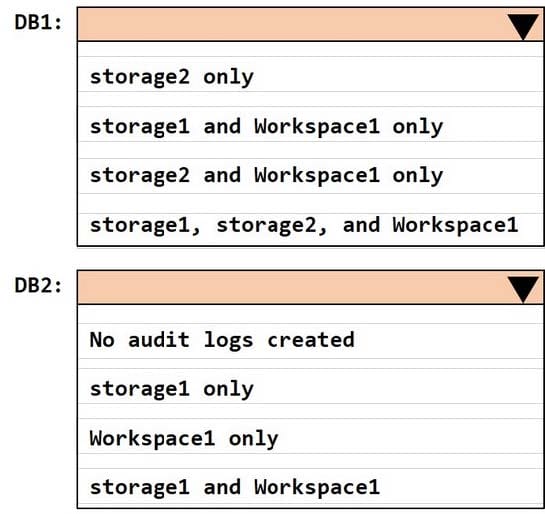
You have an Azure subscription named Sub1 that contains the Azure key vaults shown in the following table:
In Sub1, you create a virtual machine that has the following configurations:
1.
Name: VM1
2.
Size: DS2v2
3.
Resource group: RG1
4.
Region: West Europe
5.
Operating system: Windows Server 2016
You plan to enable Azure Disk Encryption on VM1.
In which key vaults can you store the encryption key for VM1?
A. Vault1 or Vault3 only
B. Vault1, Vault2, Vault3, or Vault4
C. Vault1 only
D. Vault1 or Vault2 only
You have an Azure Active Directory (Azure AD) tenant that contains a group named Group1. You need to ensure that the members of Group1 sign in by using passwordless authentication. What should you do?
A. Configure the sign-in risk policy.
B. Create a Conditional Access policy.
C. Configure the Microsoft Authenticator authentication method policy.
D. Configure the certificate-based authentication (CBA) policy.